Authentication
RADIUS Framed-IP into accounting packets (234003 189828)
RADIUS attributes, including NAS-IP-Address, Called-Station-ID, Framed-IP-Address, and Event-Timestamp, are supported.
Include RADIUS attribute CLASS in all accounting requests (290577)
RADIUS attribute CLASS in accounting requests for firewall, WiFi, and proxy authentication is now supported. RADIUS attribute CLASS is returned in Access-Accept message and it is added to all accounting requests.
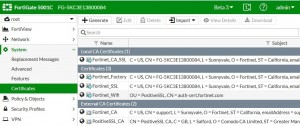
Certificate–related changes (263368)
Fortinet_factory certificate has been re-signed with an expiration date of 2038 and it is used instead of fortinet_factory2, which has been removed.
Improvements and changes to per-VDOM certificates (276403 267362)
The CA and local certificate configuration is now available per-VDOM. When an admin uploads a certificate to a VDOM, it will only be accessible inside that VDOM. When an admin uploads a certificate to global, it will be accessible to all VDOMs and global.
There are factory default certificates such as Fortinet_CA_SSL, Fortinet_SSL, PositiveSSL_CA, Fortinet_Wifi, and Fortinet_Factory, these certificates are moved to per-VDOM and automatically generated when a new VDOM is created.
The Fortinet_Firmware certificate has been removed and all the attributes that use Fortinet_Firmware now use
Fortinet_Factory.
CLI Changes
Two new attributes range and source have been added: range can be global or per-VDOM, if the certificate file is imported from global, it is a global certificate. If the certificate file is imported from a VDOM, it is VDOM certificate. source can be factory, user or fortiguard:
factory: The factory certificate file with FortiOS version, this includes: Fortinet_CA_SSL, Fortinet_SSL, PositiveSSL_CA, Fortinet_Wifi, Fortinet_Factory.
user: Certificate file imported by the user.
fortiguard: Certificate file imported from FortiGuard.
config certificate local edit Fortinet_Factory
set range global/vdom
set source factory/user/fortiguard end
end
Default Root VDOM Certificates

Certificates with the same names are also available from the global configuration. These are generated with you turn on VDOMs.