FortiGuard
FortiGuard services can be purchased and registered to your FortiGate unit. The FortiGate must be connected to the Internet in order to automatically connect to the FortiGuard Distribution Network (FDN) to validate the license and download FDN updates.
The FortiGuard subscription update services include:
- AntiVirus (AV) l Intrusion Protection Service (IPS) l Application Control l Anti-Spam l Web Filtering
- Web Application Firewall (WAF)
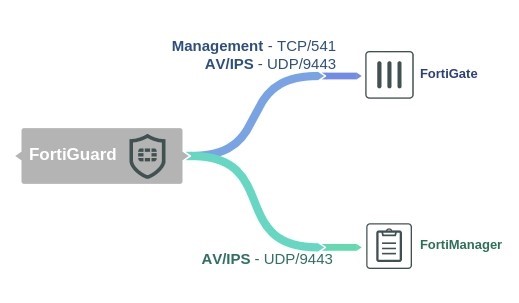
The FDN sends notice that a FortiGuard AntiVirus and IPS update is available on UDP/9443.
Enabling FDN updates and FortiGuard Services
In order to receive FortiGuard subscription updates, the unit needs to have access to the Internet and be able to connect to a DNS server in order to resolve the following URLs:
l update.fortiguard.net: For AV and IPS updates l service.fortiguard.net: For web filtering and anti-spam updates
- Go to System > FortiGuard. Under AntiVirus & IPS Updates, enable Scheduled Updates, and configure an update schedule.
- You can force the unit to connect to the AV/IPS server by selecting Update AV & IPS Definitions.
- You can view your subscription details above in the License Information
- Once the schedule has been enabled, select Apply.
To see if the service is viable, open the CLI console and enter the following commands below.
For Web Filtering:
diagnose debug rating
For Anti-Spam:
diag spamfilter fortishield servers
If only one or two IPs are displayed in the command outputs, it could be one of the following issues:
l No response from the DNS server: Either the DNS server is unreachable or there is a problem with the routing. Make sure that contact to the DNS server is available by resolving some URLs from the CLI, for example:
exec ping http://www.google.com exec ping service.fortiguard.net
You can also l Review update errors: Review update information from the last update, enable debug outputs and force the update:
diag test update info
FortiGuard
diag debug enable
diag debug application update 255 exec update-ase exec update-av exec update-ips
After troubleshooting, it is highly recommended to turn off debug mode:
diag debug disable diag debug application update 0
l FortiGuard Web filtering: Port blocking or packet inspection is occurring downstream. The default port used by the FortiGuard for the FortiGuard services is 53. The traffic will fail any DNS packet inspection that could be happening.
You can either change the port to 8888 from the GUI, or change the source port for management traffic with the following CLI command:
config system global set ip-src-port-range 1035-25000
end diag test application urlfilter 99 diag test application smtp 99
CLI Syntax
The following section contains commands to control FortiGuard.
system.autoupdate/push-update
The following command will set the FDN push update port.
config system.autoupdate push-update edit <name_str> set port <integer>
end
system.autoupdate/tunneling
The following command will set the proxy server port that the FortiGate will use to connect to the FortiGuard Distribution Network (FDN).
config system.autoupdate tunneling edit <name_str> set port <integer>
end
system/fortiguard
The following command will set the port by which scheduled FortiGuard service updates will be received.
config system fortiguard edit <name_str> set port [53 | 8888 | 80]
end
FortiGuard
webfilter/fortiguard
The following command will close ports used for HTTPS/HTTP override authentication and disable user overrides:
config webfilter fortiguard edit <name> set close-ports [enable | disable] end