It has been a lonnnnng time since I have posted. That is my fault. Sometimes you need to relax. I relaxed, a LOT and got fat in the process. I am back now! and FortiOS 6.6 which is upcoming in the next few months will have LTS (long term support) with a renewed focus on security and stability. If that doesn’t make your worm wiggle I dunno what will.
Tag Archives: fortigate
Technical Support Organization Overview
Technical Support Organization Overview
This section explains how Fortinet’s technical support works, as well as how you can easily create an account to get technical support for when issues arise that you cannot solve yourself.
This section contains the following topics:
- Fortinet Global Customer Services Organization
- Creating an account
- Registering a device
- Reporting problems
- Assisting technical support
- Support priority levels
- Return material authorization process
Fortinet Global Customer Services Organization
The Fortinet Global Customer Services Organization is composed of three regional Technical Assistance Centers (TAC):
- The Americas (AMER)
- Europe, Middle East, and Africa (EMEA)
- Asia Pacific (APAC)
The regional TACs are contacted through a global call center. Incoming service requests are then routed to the appropriate TAC. Each regional TAC delivers technical support to the customers in its regions during its hours of operation. These TACs also combine to provide seamless, around-the-clock support for all customers.
Fortinet regions and TAC
Creating an account
To receive technical support and service updates, Fortinet products in the organization must be registered. The Product Registration Form on the support website will allow the registration to be completed online. Creating an account on the support website is the first step in registering products.
Go to the Fortinet support site shown below:
Customer service and support home page
Once the support account has been created, product details can be provided by going to the Product Register/Renew and Manage Product buttons displayed on the home page. Alternately, the product registration can be completed at a later time.
Registering a device
Complete the following steps when registering a device for support purposes:
1. Log in using the Username and Password defined when the account was created
2. Under the Asset section, select Register/Renew to go to the Registration Wizard. Alternatively, use the Asset menu at the top of the page.
Register/Renew and Manage Products menu
3. Get a serial number from the back of the FortiGate unit or from the exterior of the FortiGate shipping box.
4. Enter the serial number, service contract registration code or license certificate number to start the product registration.
Adding a product to a support account
5. Enter your registration information.
6. Read and accept the license agreement.
7. Complete the verification process.
8. Select Finish to complete the registration process.
9. Registration wizard
Reporting problems
Problems can be reported to a Fortinet Technical Assistance Center in the following ways:
- By logging an online ticket
- By phoning a technical support center
Logging online tickets
Problem reporting methods differ depending on the type of customer.
Fortinet partners
Fortinet Partners are entitled to priority web-based technical support. This service is designed for partners who provide initial support to their customers and who need to open a support ticket with Fortinet on their behalf. We strongly encourage submission and follow up of support tickets using this service.
The support ticket can be submitted after logging into the partner website using one of the following links using FortiPartner account details:
This link will redirect to the general Fortinet Partner Portal extranet website. Click Support > Online Support Ticket.
https://forticare.fortinet.com/customersupport/Login/CommonLogin.aspx
Fortinet customers
There are two methods to report a technical issue on the Fortinet Support website: creating a technical support ticket by product or creating any type of ticket with the Ticket Wizard for more options.
Fortinet customers should complete the following steps to create a support ticket by product:
1. Log in to the support website at the following address with the account credentials used when the account was created: https://supporfortinet.com
2. Navigate to the top menu, click Asset and select Manage/View Products.
3. In the product list, select the product that is causing the problem.
4. On the left side bar, go to the Assistance category, and select Technical Request to create a TA Ticket.
5. Complete the Create TA Ticket fields.
6. Click View Products.
7. In the Products List, select the product that is causing the problem.
8. Complete the Create Support Ticket fields.
9. Select Finish to complete the support ticket.
Fortinet customers who would like to submit a customer service ticket, DOA ticket, RMA ticket, or FortiGuard service ticket should use the Ticket Wizard and complete the following steps:
1. Log in to the support website at the following address with the account credentials used when the account was created: https://supporfortinet.com
2. Navigate to the top menu, click Assistance and select Create a Ticket from the drop down menu.
3. Select a ticket type and complete the remaining steps in the Ticket Wizard.
4. Select Finish to complete the ticket.
Following up on online tickets
Perform the following steps to follow up on an existing issue. Partners should log into the following web site: http://partners.fortinet.com
Customers should log into the following site:
1. Log in with the account credentials used when the account was created.
2. Navigate to the top menu, click Assistance, and select Manage Tickets.
3. Use the search field on the View Tickets page to locate the tickets assigned to the account.
4. Select the appropriate ticket number. Closed tickets cannot be updated. A new ticket must be submitted if it concerns the same problem.
5. Add a New Comment or Attachment.
6. Click Submit when complete.
Every web ticket update triggers a notification to the ticket owner, or ticket queue supervisor.
Telephoning a technical support center
The Fortinet Technical Assistance Centers can also be contacted by phone. Call Fortinet Support Center at 1-408-486-7899 (international) or go to http://www.fortinet.com/support/contact_support.html and select your country from the drop-down list for local contact number.
Assisting technical support
The more information that can be provided to Fortinet technical support, the better they can assist in resolving the issue. Every new support request should contain the following information:
- A valid contact name, phone number, and email address.
- A clear and accurate problem description.
- A detailed network diagram with complete IP address schema.
- The configuration file, software version, and build number of the Fortinet device.
- Additional log files such as Antivirus log, Attack log, Event log, Debug log or similar information to include in the ticket as an attachment. If a third-party product is involved, for example, email server, FTP server, router, or switch, please provide the information on its software revision version, configuration, and brand name.
Support priority levels
Fortinet technical support assigns the following priority levels to support cases:
Priority 1
This Critical priority is assigned to support cases in which:
- The network or system is down causing customers to experience a total loss of service.
- There are continuous or frequent instabilities affecting traffic-handling capability on a significant portion of the network.
- There is a loss of connectivity or isolation to a significant portion of the network.
- This issue has created a hazard or an emergency.
Priority 2
This Major priority is assigned to support cases in which:
- The network or system event is causing intermittent impact to end customers.
- There is a loss of redundancy.
- There is a loss of routine administrative or diagnostic capability.
- There is an inability to deploy a key feature or function.
- There is a partial loss of service due to a failed hardware component.
Priority 3
This Medium priority is assigned to support cases in which:
- The network event is causing only limited impact to end customers.
- Issues seen in a test or pre-production environment exist that would normally cause adverse impact to a production network.
- The customer is making time sensitive information requests.
- There is a successful workaround in place for a higher priority issue.
Priority 4
This Minor priority is assigned to support cases in which:
- The customer is making information requests and asking standard questions about the configuration or functionality of equipment.
Customers must report Priority 1 and 2 issues by phone directly to the Fortinet EMEA Support Center. For lower priority issues, you may submit an assistance request (ticket) via the web system.
The web ticket system also provides a global overview of all ongoing support requests.
Return material authorization process
In some cases hardware issues are experienced and a replacement unit must be sent. This is referred to as a Return Material Authorization (RMA). In these cases or RMAs, the support contract must be moved to the new device. Customers can move the support contract from the failing production unit to the new device through the support web site.
To move the support contract to a new device
1. Log in to the support web site with the credentials indicated when the account was created.
2. From Manage Products, locate the serial number of the defective unit from the list of devices displayed for the account. The Product Info for the selected device will be displayed.
3. In the left side bar under the Assistance section, select RMA Transfer.
4. Enter the Original Serial Number of the original device, enter the New Serial Number, and click Replace to complete the transfer.
This will transfer the support contract from the defective unit to the new unit with the serial number provided.
Interfaces
Interfaces
Interfaces, both physical and virtual, enable traffic to flow to and from the internal network, and the Internet and between internal networks. The FortiGate unit has a number of options for setting up interfaces and groupings of subnetworks that can scale to a company’s growing requirements.
This chapter includes:
- Physical
- Interface settings
- Software switch
- Virtual Switch
- Loopback interfaces
- Redundant interfaces
- One-armed sniffer
- Aggregate Interfaces
- DHCP addressing mode on an interface
- Administrative access
- Wireless
- Interface MTU packet size
- Secondary IP addresses to an interface
- Virtual domains
- Virtual LANs
- Zones
Traffic Shaping Policies
Traffic Shaping Policies
New Traffic Shaper Policy Configuration Method (269943)
Previously, traffic shapers were configured in Policy & Objects > Objects > Traffic Shapers and then applied in security policies under Policy & Objects > Policy > IPv4 . In FortiOS 5.4, traffic shapers are now configured in a new traffic shaping section in Policy & Objects > Traffic Shapers.
The way that traffic shapers are applied to policies has changed significantly in 5.4., because there is now a specific section for traffic shaping policies in Policy & Objects > Traffic Shaping Policy. In the new traffic shaping policies, you must ensure that the Matching Criteria is the same as the security policy or policies you want to apply shaping to.
There is also added Traffic Shaper support based on the following:
- Source (Address, Local Users, Groups)
- Destination (Address, FQDN, URL or category)
- Service (General, Web Access, File Access, Email and Network services, Authentication, Remote Access, Tunneling, VoIP, Messaging and other Applications, Web Proxy)
- Application
- Application Category
- URL Category
Creating Application Control Shapers
Application Control Shapers were previously configured in the Security Profiles > Application Control section, but for simplicity they are now consolidated in the same section as the other two types of traffic shapers: Shared and Per-IP.
To create an Application Control Shaper, you must first enable application control at the policy level, in Policy
& Objects > Policy > [IPv4 or IPv6]. Then, you can create a matching application-based traffic shaping policy that will apply to it, in the new Traffic Shaping section under Policy & Objects > Traffic Shaping Policy.
New attributes added to “firewall shaping-policy” (277030) (275431)
The two new attributes are status and url-category. The status attribute verifies whether the policy is set to enabled or disabled. The url-category attribute applies the shaping-policy to sessions without a URL rating when set to 0, and no web filtering is applied.
Syntax:
config firewall shaping-policy edit 1
set status enable
set url-category [category ID number]
New button added to “Clone” Shapers
You can now easily create a copy of an existing shaper by selecting the shaper and clicking the Clone button.
I really despise Sonic Wall
Sometimes, after a long day of work, the need to vent is so powerful that you can’t overcome it. Well, today is one of those days so I figured I would bless you guys with a little bit of information. If you use a Dell Sonic Wall…..I pity you for you know not what you do….These devices are horrible. Absolutely horrible. Go buy a FortiGate, or hell, a Palo Alto even just to stay away from these things. I seriously almost shot one today with a Springfield Armory XDS 45 ACP. It would have caused and incredibly warm feeling, like that of morphine flowing through your veins, to be experienced by myself. Speaking of which, I will be filming myself shooting AND blowing up some competitor hardware as I remove them from the client’s offices. I thought you guys might get a kick out of that and lets face it, as soon as I figure out the logistics with doing it legally, I too, will enjoy it. Keep your eyes open for some Fortinet GURU how to videos. Going to start with videos based on the Cook Book, but with better explanations than what Fortinet provided and then I will move on to tasks and encounters I have seen in the field.
Remember kids, friends don’t let friends buy SonicWall.
HA heartbeat traffic set to the same priority level as data traffic
HA heartbeat traffic set to the same priority level as data traffic
Local out traffic, including HA heartbeat traffic, is now set to high priority to make sure it is processed at the same priority level as data traffic. This change has been made because HA heartbeat traffic can be processed by NP6 processors that are also processing data traffic. When HA heartbeat traffic was set to a lower priority it may have be delayed or dropped by very busy NP6 processors resulting in HA failovers.
Firewall local-in policies are supported for the dedicated HA management interface
Firewall local-in policies are supported for the dedicated HA management interface
To add local in polices for the dedicated management interface, enable ha-mgmt-inft-only and set intf to any. Enabling ha-mgmt-intf-only means the local-in policy applies only to the VDOM that contains the dedicated HA management interface.
config firewall local-in-policy
edit 0
set ha-mgmt-intf-only enable
set intf any
etc…
end
SSL Inspection – Office 365
I saw this post over on the Fortinet Support forums and wanted to cross post it here in case no one has experienced this issue. Always check the web filter and make sure domains are rated properly! Some situations it makes sense to allow websites if they are unrated or if a rating failure occurs. Especially in environments where down time hurts. Granted, I like to keep my environment more secure than that so it just makes sense for me to be quick with the troubleshooting.
Question: Hi all,
I am trying to get Office 365 to work on site behind a Fortigate 50E. Unfortunately I’m having a lot of trouble.
I found this document: http://cookbook.fortinet.com/exempting-google-ssl-inspection/
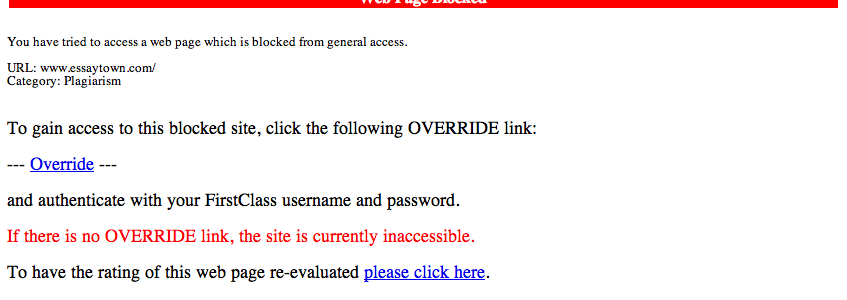
I was able to translate that into 5.4 and create the addresses that should be used by Office 365, but it still isn’t working. When I look at the IP4 policy, it appears to just be doing SSL Certificate Inspection. Do the exceptions I put into the Deep Inspection apply to SSL Certificate Inspection as well? Because that is very not clear. And if not, how do I exempt sites from SSL Certificate Inspection?
Thanks!
Correct Answer: This was actually being blocked in Webfiltering because the autodiscover.domain.com was unrated, which was set to block by default. I created an exception for it and changed the category from unrated to business IT use, and it now works.
Thanks!
