WAN types: Routing mode and Bridge mode
Before configuring the settings of a WAN port (see WAN link and WAN port) on FortiWAN for a WAN link, you need to know the connection type (we will call it WAN link type or WAN type in this document) that ISP provides you to connect to it’s network for accessing the Internet. An ISP provides the Internet access service for customers with various connection types, such as static/dynamic IP address, one/multiple IP address and routing/transparent mode. It depends on what you apply for. Different WAN types involve different mechanisms for ISP and FortiWAN to deliver network connections. When you configure a WAN port for a WAN link, you have to exactly indicate the type of the WAN link to FortiWAN so that it works in the correct way for the WAN link. FortiWAN supports the following WAN types:
l Routing Mode (See “Configurations for a WAN link in Routing Mode”) l Bridge Mode: One Static IP (See “Configurations for a WAN link in Bridge Mode: One Static IP”) l Bridge Mode: Multiple Static IP (See “Configurations for a WAN link in Bridge Mode: Multiple Static IP”) l Bridge Mode: PPPoE (See “Configurations for a WAN link in Brideg Mode: PPPoE”) l Bridge Mode: DHCP Client (See “Configurations for a WAN link in Bridge Mode: DHCP”)
This section shows you the way to recognize the WAN type of a WAN link that you apply to ISP for.
Dynamic-IP WAN link
PPPoE and DHCP are the most common ways (protocols) for ISP to assign dynamic IP addresses and provide the
Internet access service to customers. If you applied for a dynamic-IP WAN link, you can simply configure the WAN port as Bridge Mode: PPPoE or Bridge Mode: DHCP Client for the WAN link. For the two WAN types, you will not be aware of the IP address, netmask and gateway of the WAN link. ISP will provides the account and password for accessing if it is PPPoE.
Static-IP WAN link
ISP will provides you one or multiple static public IP address if you apply for a static-IP WAN link. Generally, static-IP WAN links between ISP’s central offices and customers premises could be divided into routing mode and bridge mode (transparent mode). Each involves different mechanisms. From general customer’s viewpoint, it might be not such important to distinguish between the two modes because it is a kind of back-end stuff. They could access the Internet only if they have the correct IP addresses, netmask and gateway configured. However, for FortiWAN users, it is necessary to exactly indicate the mode of the static-IP WAN link to FortiWAN so that it can cooperate with ISP for the connectivity in the correct mechanism.
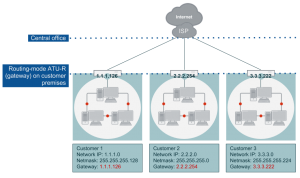
Routing mode
If you apply to ISP for a routing-mode WAN link, you will obtain an individual IP network (layer 3) which is separated from any other networks of the ISP. In that case, the ATU-R at a customer premises plays the role of a gateway to route packets between your network and the Internet. In the other words, the ATU-R connects your network with the ISP central office in routing mode. The IP addresses, default gateway and netmask that the ISP provides you can tell you whether a WAN link is routing mode or not. If the number of deducting 3 (network IP, gateway IP and broadcast IP) from the IP range that the netmask determines matches the number of usable IP addresses that ISP provides you, it means you are given a separate network, a routing-mode WAN link. For example, the ISP gives you five usable IP addresses 203.69.118.10 – 203.69.118.14, default gateway 203.69.118.9 and netmask 255.255.255.248. The netmask 255.255.255.248 divides eight IP addresses which contains five host addresses, one gateway address, one broadcast address and one address for the network ID. It just matches the number of the usable IP addresses the ISP provides. In that case you are strongly recommended to configure the WAN link on FortiWAN as Routing Mode.
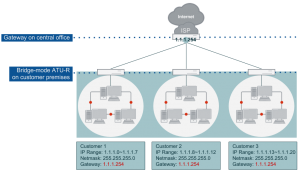
Bridge mode
Opposite to the routing mode, the ATU-R will play the role of a bridge to combine network segments (data link layer, layer 2) of customer premises and the ISP central office, if the WAN link is in bridge-mode. In that case, ISP allocates a block of IP addresses (or a network segment) of an IP network (layer 3) for you rather than a separate IP network. It implies that you and other customers (other network segments) of the ISP that in the same IP network use the same gateway, which is located at the ISP’s central office.
You can identify a bridge-mode WAN link by the IP addresses, default gateway and netmask that the ISP provides you. If the number of deducting 3 (network IP, gateway IP and broadcast IP) from the IP range that the netmask divides is larger than the number of usable IP addresses that ISP provides you, it means you are given a segment of a IP network, a bridge-mode WAN link. For example, the ISP gives you three usable IP addresses 61.88.100.1 – 61.88.100.3, default gateway 61.88.100.254 and netmask 255.255.255.0. The netmask 255.255.255.0 divides 256 IP addresses which contains 253 host addresses, one gateway address, one broadcast address and one address for the network ID. The number of host addresses that the netmask divides (253) is larger than number of IP addresses the ISP provides (3). You have to configure a WAN link to FortiWAN as Bridge Mode: One Static IP if the WAN link is in bridge-mode and ISP allocates only one IP address for you, or
Bridge Mode: Multiple Static IP if the WAN link is in bridge-mode and ISP allocates multiple IP addresses for you.
Traffic going to or coming from the near WAN (see Near WAN) is treated by FortiWAN in two different ways for routing-mode WAN link and bridge-mode WAN link. Configuring WAN links to FortiWAN as mismatched WAN type results in unexpected behaviors to traffic.
See also
l Configurations for a WAN link in Routing Mode l Configurations for a WAN link in Bridge Mode: One Static IP l Configurations for a WAN link in Bridge Mode: Multiple Static IP l Configurations for a WAN link in Brideg Mode: PPPoE l Configurations for a WAN link in Bridge Mode: DHCP
Near WAN
FortiWAN defines an area in WAN as near WAN, which traffic transferred in/from/to the area would not be counted to the WAN links. That means traffic coming from or going to near WAN through a WAN port would not be controlled by FortiWAN.
FortiWAN defines a near WAN for a WAN link in different ways between routing mode and bridge mode.
- In routing mode, the default gateway of a subnet deployed in WAN or in WAN and DMZ is near to FortiWAN. Therefore, the area between the default gateway and FortiWAN is called near WAN. In the other words, FortiWAN treats directly the subnet deployed on the WAN port as near WAN. The near WAN contains the default gateway.
- In bridge mode, the default gateway is located at ISP’s COT and the IP addresses allocated on FortiWAN are just a small part of a subnet shared with others. Therefore, only the IP addresses deployed in WAN are treated as near WAN (not include the remote gateway).
This is the reason FortiWAN separates WAN link configuration into different type: routing mode and bridge mode (See “WAN types: Routing mode and Bridge mode”). If you configure a bridge-mode WAN link that ISP provides on FortiWAN as Routing Mode and the bridge-mode WAN link might belong to a shared class C subnet, FortiWAN treats the whole class C network as near WAN, traffic goes to or comes from the class C network would be ignored for FortiWAN’s balancing, management and statistics functions. That would be a big mistake.
See also
WAN types: Routing mode and Bridge mode