How to set up your FortiWAN
These topics describe the tasks you perform to initially introduce a FortiWAN appliance to your network. These topics contain the necessary information and instructions to plan network topology, using Web UI and Configure network interfaces on FortiWAN. These topics introduce some key concepts for deploying FortiWAN, but you are assumed to have and be familiar with the fundamental concepts related networking knowledge.
Registering your FortiWAN
Before you begin, take a moment to register your Fortinet product at the Fortinet Technical Support web site: https://support.fortinet.com
Many Fortinet customer services such as firmware updates, technical support, and FortiGuard services require product registration.
For more information, see the Fortinet Knowledge Base article Registration Frequently Asked Questions.
Planning the network topology
FortiWAN is the appliance designed to perform load balancing and fault tolerance between different networks. The network environment that a FortiWAN is introducing into might be various, especially with multiple WAN links and various WAN type. A plan of network topology before adding FortiWAN recklessly into current network would be suggested to avoid damages.
Glossary for FortiWAN network setting
This glossary gives definitions of the key terms and concepts that are frequently used in the following chapters. It will be a great help for making a deployment plan, configuring and using the FortiWAN if you are clearly understand the these terms and concepts.
The glossary contains the following terms and concepts:
WAN, LAN and DMZ
Network interfaces and port mapping
WAN link and WAN port
WAN types: Routing mode and Bridge mode
Near WAN
Public IP pass through (DMZ transparent mode)
VLAN and port mapping
IPv6/IPv4 dual stack
FortiWAN in HA (High Availability) mode Scenarios to deploy subnets?
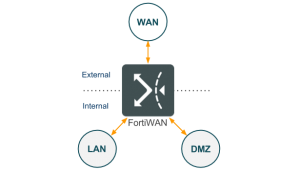
WAN, LAN and DMZ
According to the scale and purpose, a network can be defined as a Wide Area Network (WAN), Local Area Network (LAN) and Demilitarized Zone (DMZ).
- Wide Area Network: WAN (Wide Area Network) is the network that geographically covers a large area which consists of telecommunications networks. It can be simply considered the Internet as well. An internal user can communicate with the Internet via a telecommunications (called Internet Service Provider as well) network connected to FortiWAN’s WAN ports. The transmission lines can be classified as xDSL, leased line (T1, E1 and etc.), ISDN, frame relay, cable modem, FTTB, FTTH and etc.
- Local Area Network: LAN (Local Area Network) is the computer networks within a small geographical area without leased telecommunication lines involved. In this document, a LAN is considered as an internal private network which is a closed network to WAN.
- Demilitarized Zone: DMZ (Demilitarized Zone) is a local subnetwork that is separated from LAN for security issues. A DMZ is used to locate external-facing server farm which is accessible from an untrusted network (usually the Internet), but inaccessible to LAN. FortiWAN provides physical ports for the DMZ purpose.
A network site generally consists of the three basic components, WAN, LAN and DMZ. As an edge device of a network site, FortiWAN basically plays the role routing packets and provides services for communications among LAN, WAN and DMZ. The FortiWAN connects those networks (WAN, LAN and DMZ) to its network interfaces (called network ports as well) and so that the networks can communicate with each other appropriately. This involves two configurations, defining the purpose of a network port (see Network interfaces and port mapping) and correct network settings on the network port for the connected network (see Configuring Network Interface).
Network interfaces and port mapping
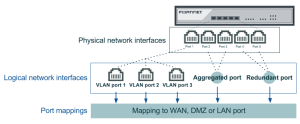
Physical network interfaces and the port mapping
The physical network ports (network interfaces) on the panel of a FortiWAN appliance are used to connect the FortiWAN with WAN, LAN and DMZ networks, so that the networks can communicate with each other. Each of the network ports can be mapped to one of the following types which differ in function:
l WAN port: is used to connect FortiWAN with a WAN network. l LAN port: is used to connect FortiWAN with a LAN network. l DMZ port: is used to connect FortiWAN with a DMZ network. l HA port: is used to connect two FortiWAN units for HA deployment (See FortiWAN in HA (High Availability) Mode).
The network port type indicates the network type (WAN, LAN or DMZ) that a network port is supposed to connect to. Most of FortiWAN’s functions, such as NAT, auto routing, firewall, bandwidth management, traffic statistics, public IP pass-through and etc., are relative to the direction of traffic flow passing through FortiWAN. It strongly requires correspondence between types of a network port and the connected network. FortiWAN might function incorrectly if a network is not corrected to a corresponding network port, for example connecting a WAN network (WAN link) to a LAN port. For the details of physical network interfaces, you can see FortiWAN Quick Start Guide.
The diagram above shows the port mapping of a FortiWAN that ports 1~3 are WAN ports, port 4 and port 5 are a LAN port and a DMZ port respectively. Port mapping can be programmed from FortiWAN’s Web UI, see Configurations for VLAN and Port Mapping.
Note: To make a FortiWAN operate correctly with the connected networks, it requires not only the correspondence between types of network ports and the connected networks, but also corresponding configurations to the network port (see Configuring Network Interface).
Default port mappings
Except the HA port, each of the physical network ports can be programmed as WAN, LAN or DMZ via Web UI. However, for the first time you access the Web UI (see Connecting to the web UI and the CLI), you probably need to know the default port mapping so that you can access the correct network port for Web UI. All the network ports on the panel of FortiWAN appliance are numbered, and the default mappings are as follows:
| Model | Ports Supported | WAN Ports | LAN
Port |
DMZ
Port |
| FWN 200B | 5 GE RJ45 ports | Port 1 ~ Port 3 | Port 4 | Port 5 |
| FWN 1000B | 3 GE RJ45 ports and 4 GE SFP ports | Port 1 ~ Port 5 | Port 6 | Port 7 |
| FWN 3000B | 8 GE RJ45 ports, 8 GE SFP ports and 8 10GE SFP+ ports | Port 1 ~ Port 10 | Port 11 | Port 12 |
| FWN VM | 10 vNICs | vNIC 2 | vNIC 3 | vNIC 4 |
FortiWAN 3000B’s Prot 13 ~ Port 24 and FortiWAN VM’s vNIC 5 ~ vNIC 10 are undefined by default, they can be defined via Web UI (see VLAN and Port Mapping). After logging onto the Web UI, you can also check and program the network port mapping on System > Network Setting > VLAN and Port Mapping.
Logical network interfaces
For extension, aggregation and redundancy, you can create multiple VLAN ports on a physical network interface, and an aggregated or a redundant port on any pair of the physical network interfaces. Each of the created logical network interfaces can be programmed as WAN, LAN or DMZ port (whether a physical or a logical port, the port type must be defined to connect the network port with a network). FortiWAN supports the IEEE 802.1Q for VLAN tagging and the IEEE 802.3ad for port aggregation (see Configurations for VLAN and Port Mapping).
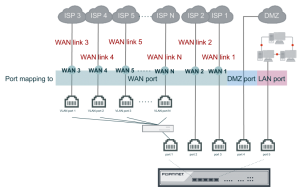
WAN link and WAN port
A FortiWAN appliance has limited physical network interfaces (ports) depending on the models, but unlimited logical network interfaces (ports) can be created on the physical ports. With correct port mappings, FortiWAN can connect to more networks than the supported number of physical ports.
As previous description, whether a physical or a logical network interface, it requires the network interface mapped to a port type (WAN, DMZ or LAN) for connecting to corresponding network type. A WAN port is a physical or logical network port that is port mapped to the WAN type. A WAN link is a connectivity between a FortiWAN and an ISP network. Actually, a WAN link connects a WAN port of FortiWAN with the remote device (modem or ATU-R) of an ISP, so that the internal networks and the Internet can communicate to each other through the WAN link. A WAN link requires corresponding settings on the WAN port. Configuration of a WAN port contains the information provided by the ISP, such as the IP addresses, default gateway, network mask or username/password, it depends on the WAN link type you apply to the ISP (See “WAN types: Routing mode and Bridge mode”). You will see the two terms, WAN link and WAN port, frequently in this document.
For purposes of traffic load balancing and fault tolerance, you will need multiple WAN links to connect to the Internet. In case that the WAN links demanded are more that the physical network ports of a FortiWAN appliance in quantity, you can have enough WAN ports for the WAN links by creating multiple logical network ports (VLAN ports) on a physical port (See “Configurations for VLAN and Port Mapping”). Although you can create VLAN ports on a physical port without limitation in quantity, FortiWAN supports limited WAN links. FortiWAN 200B supports up to 25 WAN links, FortiWAN 1000B and 3000B support up to 50 WAN links, even if you create more than 50 VLAN ports. These WAN links are named with numbers, such as WAN 1, WAN 2 and WAN 3. You will see this when you configure settings of a WAN port (See “Configuring your WAN”).
The above diagram shows how to create N WAN ports (WAN 1 ~ WAN N) through the three physical network ports of a FortiWAN. Two of the WAN ports use two of the physical network ports and the rest of the WAN ports use the VLAN ports. The N WAN links connect the N WAN ports with N ISP networks. Traffic of WAN link 1 and 2 will be transferred through physical port 2 and port 3 respectively, and traffic of the remaining WAN link (WAN link 3 ~ WAN link N) will be transferred through physical port 1.
See also
Configurations for VLAN and Port Mapping


Gee thank you for this..great content