LAN Private Subnet
[LAN Private Subnet] is the second most important part for deploying FortiWAN in your network. In contrast with configurations on WAN Settings to active the WAN link transmission from FortiWAN to Internet (external network), LAN Private Subnet is the configuration for deploying the internal network on FortiWAN’s LAN ports. There are two parts for setting LAN private subnet: Basic Subnet and Static Routing Subnet, which respectively are the subnets connected directly to FortiWAN’s LAN ports and the subnets connected indirectly to FortiWAN via a router. (See “Scenarios to deploy subnets”)
Basic Subnet
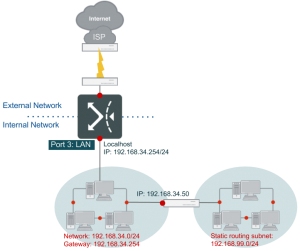
Here is a simple example to demonstrate a configuration for the basic subnet in the typical LAN environment.
As the illustration, FortiWAN port3 has been mapped to LAN port via [System / Network Setting / VLAN and Port Mapping] (See “VLAN and Port Mapping”), and is assigned with private IP 192.168.34.254. Enter this IP address in the field [IP(s) on Localhost]. For hosts in LAN, port3 (192.168.34.254) serves as gateway as well. Enter the netmask (255.255.255.0) for the subnet in the field [Netmask]. Select the LAN port.
| IPv4 Basic Subnet | |
| IP(s) on Localhost | 192.168.34.254 |
| Netmask | 255.255.255.0 |
| LAN Port | Port3 |
Check the field in [Enable DHCP], to allocate IP address (any of 192.168.34.175~192.168.34.199) dynamically via DHCP to PCs in LAN. If any host in LAN requires static IP addresses, then enter in [Static Mapping] the IP addresses to designate, and MAC addresses of the PCs as well. Check the field in [NAT Subnet for VS], which is an optional choice. When users in LAN or DMZ access the WAN IP of virtual server, their packets may bypass FortiWAN and flow to internal server directly. This function can translate the source IP address of the users’ packets into IP address of FortiWAN, to ensure the packets flow through FortiWAN. If no check is made, the system will determine which IP address it may translate into by itself. Similarly, to deploy an IPv6 private LAN on FortiWAN port4 which has been mapped to LAN port, with IPv6 address 2001:a:b:cd08::1 served as gateway for PCs in LAN. Check the field in [Enable SLAAC] or [Enable DHCPv6 Service] to allocate IP addresses dynamically to PCs in LAN. [NAT Subnet for VS] is not supported in IPv6 private LAN. The SLAAC and DHCPv6 in FortiWAN are designed to work together, which the SLAAC responses router advertisement (including default gateway and DNS server) to a host and DHCPv6 responses the host an appropriate IPv6 address.
For the details about DHCP, DHCP Relay, SLAAC and DHCPv6, see “Automatic addressing within a basic subnet”.
Static Routing Subnet
[Static Routing Subnet] is useful when in LAN a router .is used to cut out a separate subnet which does not connect to FortiWAN directly. The topology is similar to [Static Routing Subnet: Subnet in DMZ] mentioned previously, and the only difference is this example is set in LAN rather than in DMZ. In this topology below, a subnet 192.168.99.x is located in the LAN and connects to router 192.168.34.50, while another subnet 192.168.34.x is located on the LAN port as well, but connects to FortiWAN directly. The configurations here indicate how FortiWAN to route packets to subnet 192.168.99.x.
| IPv4 Static Routing Subnet | |
| Network IP | 192.168.99.0 |
| Netmask | 255.255.255.0 |
| Gateway | 192.168.34.50 |
RIP
FortiWAN supports the Routing Information Protocol (RIP v1, v2), RIP employs hot count as the metric, and uses timer broadcast to update the router. As RIP features configuration simplicity and operation convenience, it has been widely used across all fields. RIP version 1 (v1)1 was designed to suit the dynamic routing needs of LAN technology-based IP internetworks, and to address some problems associated with RIP v1, a refined RIP, RIP version 2 (v2) was defined. RIP v2 supports sending RIP announcements to the IP multicast address and supports the use of authentication mechanisms to verify the origin of incoming RIP announcements.
Check the field in [RIP] if you have enabled RIP on your private subnet router. Check the field in [RIP v1] if you have enabled RIP v1 on your private subnet router behind FortiWAN. Thus, FortiWAN can forward packets from the RIP v1-enabled private subnet. Otherwise, check the field in [RIP v2] if you have enabled RIP v2 on your private subnet router. Thus, FortiWAN can forward RIP v2 packets. Moreover, if you have enabled RIP v2 authentication, type the password in [Password]. Otherwise, keep [Password] blank.
OSPF
Apart from RIP, FortiWAN also supports OSPF (Open Shortest Path First), to assign LAN port router with given preference. Like RIP, OSPF is designated by the Internet Engineering Task Force (IETF) as one of several Interior Gateway Protocols (IGPs). Rather than simply counting the number of hops, OSPF bases its path descriptions on “link states” that take into account additional network information. Using OSPF, a host that obtains a change to a routing table or detects a change in the network immediately multicasts the information to all other hosts in the network so that all will have the same routing table information.
| OSPF Interface | Displays the LAN port in the network. Check the box to enable OSPF over the port. |
| Area Setting | Network is logically divided into a number of areas based on subnets.
Administrators can configure area ID, which accepts numbers or IPs only. |
| Authentication Setting | Routers in different areas require authentication to communicate with each other. Authentication types: Null, Simple Text Password, MD5. |
| Router Priority | Set router priority. Router that sends the highest OSPF priority becomes DR (Designated Router). The value of the OSPF Router Priority can be a number between 0 and 255. |
| Hello Interval | Set the interval, in seconds, to instruct the router to send out OSPF keepalive packets to inform the other routers. |
| Dead Interval | Set the length of time, in seconds, that OSPF neighbors will wait without receiving an OSPF keepalive packet from a neighbor before declaring the neighbor router is down. |
| Retransmit Interval | Set the interval, in seconds, between retransmissions of Link ups. When routers fail to transmit hello packets, it will retransmit packets in the defined interval. |
| Authentication Type | This specifies whether the router will perform authentication of data passing the LAN. Choices are: Null, Simple Text Password, MD5. |
FortiWAN provides statistics for the RIP & OSPF service, see “RIP & OSPF Status”.
VRRP
VRRP is a Virtual Router Redundancy Protocol that runs on a LAN port. A system can switch between VRRP or HA mode; when switched, the system will reboot first for changes to take effect. When VRRP mode is enabled, the HA mode will be automatically disabled, and also a VRID field will appear available for input in [VLAN and Port Mapping] setting page (See “VLAN and Port Mapping”). In general, VRRP is faster in detecting the master unit compared to HA mode. Although FortiWAN’s VRRP implementation is based on VRRP version 3, some restrictions may apply:
- Always in non-preempt mode. l Always in non-accept mode.
- IPv6 is not supported. l Active-active mode is not supported.
When FortiWAN switches to master mode, it automatically starts WAN link health detection. When it switches to backup mode, it automatically stops WAN link health detection and sets WAN status to “failed”.
In addition, DHCP servers in LAN and DMZ should let clients use FortiWAN virtual IP and the default gateway (as FortiWAN’s DHCP service does). If RIP and OSPF is used in LAN, FortiWAN uses real IP at OSPF and virtual IP at RIP to exchange route information. Clone-MAC settings will be ignored if VRRP function is enabled. FortiWAN doesn’t exchange NAT table with VRRP peers. When VRRP master changes, existing connection might break.
| Local Priority | The priority field specifies the sending VRRP router’s priority for the virtual router. Select a number from 1 to 254 as the priority for the VR. |
| Advertisement Interval | Set the time interval in centi-seconds between advertisements. (Default is 100) |
| Virtual address | Enter a virtual IP address for the virtual router. |
| Double-check Link | Click the checkbox to enable. When enabled, the backup router will check whether the master is responding ARP on the specified WAN port. |
See also
- Scenarios to deploy subnets
- VLAN and Port Mapping
- Summary
- RIP & OSPF Status