FortiSandbox Integration
The following improvements have been made to how sandboxing, using either a FortiSandbox Appliance or
FortiCloud Sandboxing, integrates with a FortiGate unit.
See the Cookbook recipe Sandboxing with FortiSandbox and FortiClient.
Connecting to a FortiSandbox
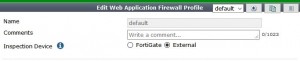
1. Go to System > External Security Devices and select Enable Sandbox Inspection.
2. You can either select FortiSandbox Appliance or FortiSandbox Cloud.
3. If you select FortiSandbox Appliance, add the Server IP address.
4. Select Test Connectivity to verify that you can connect to FortiSandbox.
5. Then edit an AntiVirus profile by going to Security Profiles > AntiVirus and selecting Send Filter to
FortiSandbox Appliance for Inspection.
6. You can also select to send Suspicious Files, Executable files or all supported files.
7. Select Use FortiSandbox Database to add signatures for suspicious files found by FortiSandbox to your
FortiGate antivirus signature database.
8. Then select this Antivirus profile in a firewall policy to send files in traffic accepted by the firewall policy to
FortiSandbox.
9. You can also go to Security Profiles > Web Filter and select Block malicious URLs discovered by
FortiSandbox.
Pushing malicious URLs to Web Filtering
The malicious URL database contains all malicious URLs active in the last month. The FortiSandbox can add the URLs where any malicious files originated to a URL filter, to block these files from being downloaded again from that URL.
This feature is enabled in a Web Filter profile under Security Profiles > Web Filter > Block malicious URLs discovered by FortiSandbox.
CLI Syntax
config webfilter profile edit <profile>
config web
…
set blacklist [enable | disable]
… end
Files blocked by a FortiSandbox signature can be viewed and filtered for in the FortiSandbox dashboard. Information on the current database for both malware signatures and blocked URLs can be found by going to System > External Security Devices.
FortiSandbox Dashboard in FortiView
The FortiSandbox dashboard is available from FortiView > FortiSandbox. The dashboard shows all samples submitted for sandboxing. Information on the dashboard can be filtered by checksum, file name, result, source, status, and user name. Each entry also offers a drilldown view to show more details about a particular sample.