Preventing the explicit web proxy from changing source addresses
By default in NAT/Route mode the explicit web proxy changes the source address of packets leaving the FortiGate to the IP address of the FortiGate interface that the packets are exiting from. In Transparent mode the source address is changed to the management IP.
This configuration hides the IP addresses of clients and allows packets to return to the FortiGate unit interface without having to route packets from clients. You can use the following command to configure the explicit web proxy to keep the original client’s source IP address:
config firewall explicit-proxy-policy edit 0
set proxy web
set transparent enable end
Example users on an internal network browsing the Internet through the explicit web proxy with web caching, RADIUS authentication, web filtering, and virus scanning
This example describes how to configure the explicit web proxy for the example network shown below. In this example, users on the internal network connect to the explicit web proxy through the Internal interface of the FortiGate unit. The explicit web proxy is configured to use port 8888 so users must configure their web browser proxy settings to use port 8888 and IP address 10.31.101.100.
Example explicit web proxy network topology

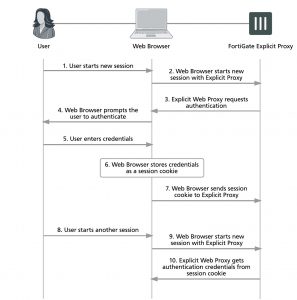
Explicit web proxy users must authenticate with a RADIUS server before getting access to the proxy. The explicit proxy policy that accepts explicit web proxy traffic applies per session authentication and includes a RADIUS server user group. The authentication rule also applies web filtering and virus scanning.
General configuration steps
This section breaks down the configuration for this example into smaller procedures. For best results, follow the procedures in the order given:
1. Enable the explicit web proxy for HTTP and HTTPS and change the HTTP and HTTPS ports to 8888.
2. Enable the explicit web proxy on the internal interface.
3. Add a RADIUS server and user group for the explicit web proxy.
4. Add an authentication explicit proxy policy. Enable web caching. Add an authentication rule and enable antivirus and web filtering.
Configuring the explicit web proxy – web-based manager
Use the following steps to configure the explicit web proxy.
To enable and configure the explicit web proxy
1. Go to System > Feature Select and turn on the Explicit Proxy feature.
2. Go to Network > Explicit Proxy and change the following settings:
Enable Explicit Web Proxy Select HTTP/HTTPS.
Listen on Interfaces No change. This field will eventually show that the explicit web proxy is enabled for the Internal interface.
HTTP Port 8888
HTTPS Port 0
Realm You are authenticating with the explicit web proxy.
Default Firewall Policy
Action Deny
3. Select Apply.
To enable the explicit web proxy on the Internal interface
1. Go to Network > Interfaces.
2. Edit the internal interface.
3. Select Enable Explicit Web Proxy.
4. Select OK.
To add a RADIUS server and user group for the explicit web proxy
1. Go to User & Device > RADIUS Servers and select Create New to add a new RADIUS server:
Name RADIUS_1
Primary Server Name/IP 10.31.101.200
Primary Server Secret RADIUS_server_secret
2. Select OK.
3. Go to User & Device > User Groups and select Create New to add a new user group.
Name Explict_proxy_user_group
Type Firewall
Remote Groups RADIUS_1
Group Name Any
4. Select OK.
To add an explicit proxy policy
1. Go to Policy & Objects > Addresses and select Create New.
2. Add a firewall address for the internal network:
Category Address
Name Internal_subnet
Type Subnet / IP Range
Subnet / IP Range 10.31.101.0
Interface Any
3. Go to Policy & Objects > Explicit Proxy Policy and select Create New.
4. Configure the explicit web proxy policy.
Explicit Proxy Type Web
Source Address Internal_subnet
Outgoing Interface wan1
Destination Address all
Action AUTHENTICATE
5. Under Configure Authentication Rules select Create New to add an authentication rule:
Groups Explicit_policy
Source User(s) Leave blank
Schedule always
6. Turn on Antivirus and Web Filter and select the default profiles for both.
7. Select the default proxy options profile.
8. Select OK.
9. Make sure Enable IP Based Authentication is not selected.
10. Turn on Web Cache.
11. Select OK.
Configuring the explicit web proxy – CLI
Use the following steps to configure the example explicit web proxy configuration from the CLI.
To enable the explicit web proxy on the Internal interface
1. Enter the following command to enable the explicit web proxy on the internal interface.
config system interface edit internal
set explicit-web-proxy enable
end
To enable and configure the explicit web proxy
1. Enter the following command to enable the explicit web proxy and set the TCP port that proxy accepts HTTP and
HTTPS connections on to 8888.
config web-proxy explicit set status enable
set http-incoming-port 8888 set https-incoming-port 8888
set realm “You are authenticating with the explicit web proxy” set sec-default-action deny
end
To add a RADIUS server and user group for the explicit web proxy
1. Enter the following command to add a RADIUS server:
config user radius edit RADIUS_1
set server 10.31.101.200
set secret RADIUS_server_secret
end
2. Enter the following command to add a user group for the RADIUS server.
config user group
edit Explicit_proxy_user_group set group-type firewall
set member RADIUS_1
end
To add a security policy for the explicit web proxy
1. Enter the following command to add a firewall address for the internal subnet:
config firewall address edit Internal_subnet
set type iprange
set start-ip 10.31.101.1 set end-ip 10.31.101.255
end
2. Enter the following command to add the explicit web proxy security policy:
config firewall explicit-proxy-policy edit 0
set proxy web
set dstintf wan1
set srcaddr Internal_subnet set dstaddr all
set action accept
set service webproxy set webcache enable
set identity-based enable set ipbased disable
end
set active-auth-method basic config identity-based-policy
edit 0
set groups Explicit_Proxy_user_group set schedule always
set utm-status enable set av-profile default
set webfilter-profile default
set profile-protocol-options default end
Testing and troubleshooting the configuration
You can use the following steps to verify that the explicit web proxy configuration is working as expected:
To test the explicit web proxy configuration
1. Configure a web browser on the internal subnet to use a web proxy server at IP address 10.31.101.100 and port 8888.
2. Browse to an Internet web page.
The web browser should pop up an authentication window that includes the phrase that you added to the Realm option.
3. Enter the username and password for an account on the RADIUS server.
If the account is valid you should be allowed to browse web pages on the Internet.
4. Close the browser and clear its cache and cookies.
5. Restart the browser and connect to the Internet.
You could also start a second web browser on the same PC. Or you could start a new instance of the same browser as long as the browser asks for a user name and password again.
You should have to authenticate again because identity-based policies are set to session-based authentication.
6. If this basic functionality does not work, check your FortiGate and web browser configuration settings.
7. Browse to a URL on the URL filter list and confirm that the web page is blocked.
8. Browse to http://eicar.org and attempt to download an anti-malware test file.
The antivirus configuration should block the file.
Sessions for web-proxy security policies do not appear on the Top Sessions dashboard widget and the count column for security policies does not display a count for explicit web proxy security policies.
9. You can use the following command to display explicit web proxy sessions
get test wad 60
IP based users:
Session based users:
user:0x9c20778, username:User1, vf_id:0, ref_cnt:9
Total allocated user:1
Total user count:3, shared user quota:50, shared user count:3
This command output shows one explicit proxy user with user name User1 authenticated using session-based authentication.