Explicit web proxy authentication
You can add authentication to explicit web proxy policies to control access to the explicit web proxy and to identify users and apply different UTM features to different users.
Authentication of web proxy sessions uses HTTP basic and digest authentication as described in RFC 2617 (HTTP Authentication: Basic and Digest Access Authentication) and prompts the user for credentials from the browser allowing individual users to be identified by their web browser instead of IP address. HTTP authentication allows the FortiGate unit to distinguish between multiple users accessing services from a shared IP address.
You can also select IP-based authentication to authenticate users according to their source IP address in the same way as normal firewall policies.
IP–Based authentication
IP-based authentication applies authentication by source IP address. For the explicit web proxy, IP authentication is compatible with basic, digest, NTLM, FSSO, or RSSO authentication methods. Once a user authenticates, all sessions to the explicit web proxy from that user’s IP address are assumed to be from that user and are accepted until the authentication timeout ends or the session times out.
This method of authentication is similar to standard (non-web proxy) firewall authentication and may not produce the desired results if multiple users share IP addresses (such as in a network that uses virtualization solutions or includes a NAT device between the users and the explicit web proxy).
To configure IP-based authentication, add an explicit web proxy security policy, set the Action to AUTHENTICATION, and select Enable IP Based Authentication is selected.
Use the following CLI command to add IP-based authentication to a web proxy security policy. IP-based authentication is selected by setting ip-based to enable.
config firewall explicit-proxy-policy edit 0
set proxy web
set scraddr User_network set dstintf port1
set dstaddr all set action accept
set identity-based enable set ip-based enable
config identity-based-policy edit 0
set groups Internal_users set users dwhite rlee
set schedule always end
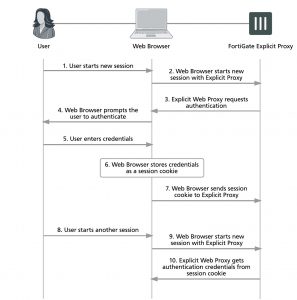
Per session authentication
If you don’t select IP Based the explicit web proxy applies HTTP authentication per session. This authentication is browser-based. When a user enters a user name and password in their browser to authenticate with the explicit web proxy, this information is stored by the browser in a session cookie. Each new session started by the same web browser uses the session cookie for authentication. When the session cookie expires the user has to re- authenticate. If the user starts another browser on the same PC or closes and then re-opens their browser they have to authenticate again.
Since the authentication is browser-based, multiple clients with the same IP address can authenticate with the proxy using their own credentials. HTTP authentication provides authentication for multiple user sessions from the same source IP address. This can happen if there is a NAT device between the users and the FortiGate unit. HTTP authentication also supports authentication for other configurations that share one IP address among multiple users. These includes Citrix products and Windows Terminal Server and other similar virtualization solutions.
To configure per session authentication, add a explicit web proxy policy, set the Action to AUTHENTICATE, and make sure Enable IP Based Authentication is not selected.
Use the following CLI command to add per session authentication to a security policy. Per session authentication is selected by setting ip-based to disable.
config firewall explicit-proxy-policy edit 0
set proxy web
set scraddr User_network set dstintf port1
set dstaddr all set action accept
set identity-based enable set ip-based disable
config identity-based-policy edit 0
set groups Internal_users set users dwhite rlee
set schedule always end
end
Per session HTTP authentication
Transaction-based authentication
Multiple HTTP transactions (request/response) may be pipelined in the same TCP connection. Typically, all HTTP transactions of a TCP connection are considered as belonging to the same user. However, some devices (e.g., load balancers) may send HTTP transactions of different users to the same TCP connection and to explicit
proxy. In order to support this deployment case, transaction-based authentication can be implemented to require each HTTP transaction to be authenticated separately.
To implement transaction-based authentication in the CLI:
config firewall explicit-proxy-policy edit <id>
set transaction-based enable next
end

Have you try explicit proxy authentication with 5.6 ?
In my case it doesn’ t work, fortigate does not prompt for user and password, i have always access denied: The page you requested has been blocked by a firewall policy restriction.
With 5.4 all works perfectly.
5.6 has a ways to go before I would consider it ready for production
Have you tryed explicit proxy authentication with 5.2 ?
Testing from a citrix server