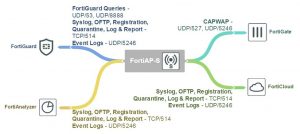
FortiAP–S Open Ports Diagram
Yearly Archives: 2017
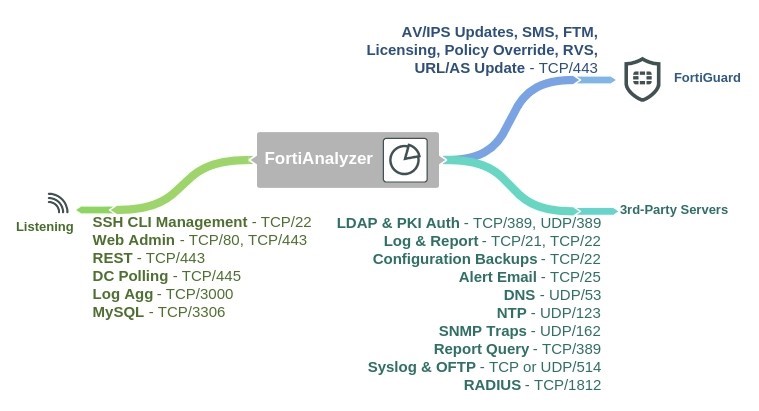
FortiAnalyzer Open Ports Diagram
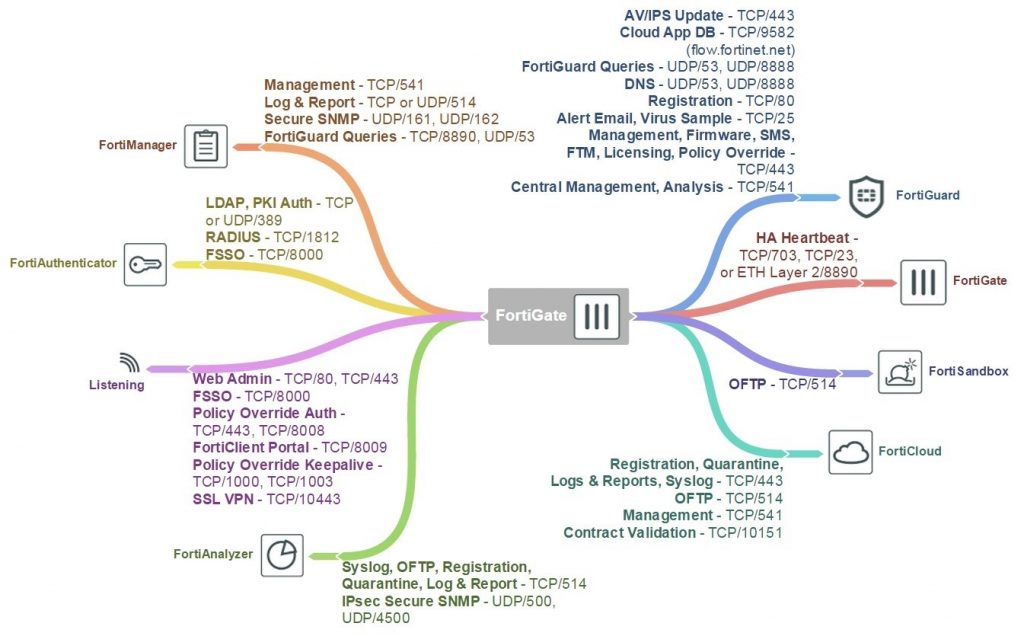
FortiGate Open Ports Diagram
WCCP Diagnose commands
Diagnose commands
The following get and diagnose commands are available for troubleshooting WAN optimization, web cache, explicit proxy and WCCP.
get test {wad | wccpd} <test_level>
Display usage information about WAN optimization, explicit proxy, web cache, and WCCP applications. Use <test_level> to display different information.
get test wad <test_level>
get test wccpd <test_level>
Variable Description
wad Display information about WAN optimization, web caching, the explicit web proxy, and the explicit FTP proxy.
wccpd Display information about the WCCP application.
Examples
Enter the following command to display WAN optimization tunnel protocol statistics. The http tunnel and tcp tunnel parts of the command output below shows that WAN optimization has been processing HTTP and TCP packets.
get test wad 1
WAD manager process status: pid=113 n_workers=1 ndebug_workers=0
Enter the following command to display all test options:
get test wad
WAD process 82 test usage:
1: display process status
2: display total memory usage.
99: restart all WAD processes
1000: List all WAD processes.
1001: dispaly debug level name and values
1002: dispaly status of WANOpt storages
1068: Enable debug for all WAD workers.
1069: Disable debug for all WAD workers.
2yxx: Set No. xx process of type y as diagnosis process.
3: display all fix-sized advanced memory stats
4: display all fix-sized advanced memory stats in details
500000..599999: cmem bucket stats (599999 for usage)
800..899: mem_diag commands (800 for help & usage)
800000..899999: mem_diag commands with 1 arg (800 for help & usage)
80000000..89999999: mem_diag commands with 2 args (800 for help & usage)
60: show debug stats.
61: discard all wad debug info that is currently pending
62xxx: set xxxM maximum ouput buffer size for WAD debug. 0, set back to default.
68: Enable process debug
69: Disable process debug
98: gracefully stopping WAD process
9xx: Set xx workers(0: default based on user configuration.)
Troubleshooting WCCP
Troubleshooting WCCP
Two types of debug commands are available for debugging or troubleshooting a WCCP connection between a FortiGate unit operating as a WCCP router and its WCCP cache engines.
Real time debugging
The following commands can capture live WCCP messages:
diag debug en
diag debug application wccpd <debug level>
Application debugging
The following commands display information about WCCP operations:
get test wccpd <integer>
diag test application wccpd <integer>
Where <integer> is a value between 1 and 6:
1. Display WCCP stats
2. Display WCCP config
3. Display WCCP cache servers
4. Display WCCP services
5. Display WCCP assignment
6. Display WCCP cache status
Enter the following command to view debugging output:
diag test application wccpd 3
Sample output from a successful WCCP connection:
service-0 in vdom-root: num=1, usable=1 cache server ID:
len=44, addr=172.16.78.8, weight=4135, status=0 rcv_id=6547, usable=1, fm=1, nq=0, dev=3(k3), to=192.168.11.55
ch_no=0, num_router=1:
192.168.11.55
Sample output from the same command from an unsuccessful WCCP connection (because of a service group password mismatch):
service-0 in vdom-root: num=0, usable=0 diag debug application wccpd -1
Sample output:
wccp_on_recv()-98: vdom-root recv: num=160, dev=3(3),
172.16.78.8->192.168.11.55
wccp2_receive_pkt()-1124: len=160, type=10, ver=0200, length=152
wccp2_receive_pkt()-1150: found component:t=0, len=20 wccp2_receive_pkt()-1150: found component:t=1, len=24 wccp2_receive_pkt()-1150: found component:t=3, len=44 wccp2_receive_pkt()-1150: found component:t=5, len=20 wccp2_receive_pkt()-1150: found component:t=8, len=24 wccp2_check_security_info()-326: MD5 check failed
WCCP packet flow
WCCP packet flow
The following packet flow sequence assumes you have configured a FortiGate unit to be a WCCP server and one or more FortiGate units to be WCCP clients.
1. A user’s web browser sends a request for web content.
2. The FortiGate unit configured as a WCCP server includes a security policy that intercepts the request and forwards it to a WCCP client.
The security policy can apply UTM features to traffic accepted by the policy.
3. The WCCP client receives the WCCP session.
4. The client either returns requested content to the WCCP server if it is already cached, or connects to the destination web server, receives and caches the content and then returns it to the WCCP server.
5. The WCCP server returns the requested content to the user’s web browser.
6. The WCCP router returns the request to the client web browser.
The client we browser is not aware that all this is taking place and does not have to be configured to use a web proxy.
Configuring the forward and return methods and adding authentication
The WCCP forwarding method determines how intercepted traffic is transmitted from the WCCP router to the WCCP cache engine. There are two different forwarding methods:
- GRE forwarding (the default) encapsulates the intercepted packet in an IP GRE header with a source IP address of the WCCP router and a destination IP address of the target WCCP cache engine. The results is a tunnel that allows the WCCP router to be multiple hops away from the WCCP cache server.
- L2 forwarding rewrites the destination MAC address of the intercepted packet to match the MAC address of the target WCCP cache engine. L2 forwarding requires that the WCCP router is Layer 2 adjacent to the WCCP client.
You can use the following command on a FortiGate unit configured as a WCCP router to change the forward and return methods to L2:
config system wccp edit 1
set forward-method L2 set return-method L2
end
You can also set the forward and return methods to any in order to match the cache server configuration.
By default the WCCP communication between the router and cache servers is unencrypted. If you are concerned about attackers sniffing the information in the WCCP stream you can use the following command to enable hash- based authentication of the WCCP traffic. You must enable authentication on the router and the cache engines and all must have the same password.
config system wccp edit 1
set authentication enable set password <password>
end
Example caching HTTP sessions on port 80 and HTTPS sessions on port 443 using WCCP
Example caching HTTP sessions on port 80 and HTTPS sessions on port 443 using WCCP
This example configuration is the same as thatdescribed in Example caching HTTP sessions on port 80 using WCCP on page 2948 except that WCCP now also cached HTTPS traffic on port 443. To cache HTTP and HTTPS traffic the WCCP service group must have a service ID in the range 51 to 255 and you must specify port 80 and 443 and protocol 6 in the service group configuration of the WCCP client.
Also the security policy on the WCCP_srv that accepts sessions from the internal network to be cached must accept HTTP and HTTPS sessions.
Configuring the WCCP server (WCCP_srv)
Use the following steps to configure WCCP_srv as the WCCP server for the example network. The example steps only describe the WCCP-related configuration.
To configure WCCP_srv as a WCCP server
1. Add a port2 to port1 security policy that accepts HTTP traffic on port 80 and HTTPS traffic on port 443 and is configured for WCCP:
config firewall policy edit 0
set srtintf port2 set dstintf port1 set srcaddr all set dstaddr all set action accept
set schedule always
set service HTTP HTTPS
set wccp enable set nat enable
end
2. Add another port2 to port1 security policy to allow all other traffic to connect to the Internet.
config firewall policy edit 0
set srtintf port2 set dstintf port1 set srcaddr all set dstaddr all set action accept
set schedule always set service ANY
set nat enable end
3. Move this policy below the WCCP policy in the port2 to port1 policy list.
4. Enable WCCP on the port5 interface.
config system interface edit port5
set wccp enable end
5. Add a WCCP service group with service ID 90 (can be any number between 51 and 255).
config system wccp edit 90
set router-id 10.51.101.100
set server-list 10.51.101.0 255.255.255.0 end
6. Add a firewall address and security policy to allow the WCCP_client to connect to the internet.
config firewall address edit WCCP_client_addr
set subnet 10.51.101.10 end
config firewall policy edit 0
set srtintf port5 set dstintf port1
set srcaddr WCCP_client_addr set dstaddr all
set action accept set schedule always set service ANY
set nat enable end
Configuring the WCCP client (WCCP_client)
Use the following steps to configure WCCP_client as the WCCP client for the example network. The example steps only describe the WCCP-related configuration.
To configure WCCP_client as a WCCP client
1. Configure WCCP_client to operate as a WCCP client.
config system settings
set wccp-cache-engine enable end
You cannot enter the wccp-cache-engine enable command if you have already added a WCCP service group. When you enter this command an interface named w.<vdom_name> is added to the FortiGate configuration (for example w.root). All traffic redirected from a WCCP router is considered to be received at this interface of the FortiGate unit operating as a WCCP client. A default route to this interface with lowest priority is added.
2. Enable WCCP on the port1 interface.
config system interface edit port1
set wccp enable
end
3. Add a WCCP service group with service ID 90. This service group also specifies to cache sessions on ports 80 and
443 (for HTTP and HTTPS) and protocol number 6.
config system wccp edit 90
set cache-id 10.51.101.10
set router-list 10.51.101.100 ports 80 443
set protocol 6 end