Automatic addressing within a basic subnet
FortiWAN functions for various network topologies which consists of connectivity of multiple subnets (basic subnet). Deployments of basic subnets varies for purposes, but they can be simply divided, according to the location, into three basic types: WAN-sided subnet, DMZ-sided subnet and LAN-sided subnet, which are supposed to connect to the WAN port, DMZ port and LAN port of FortiWAN. FortiWAN so that services the hosts in the subnets. For this reason, mechanisms to automatically address the hosts in those basic subnets are provided. FortiWAN’s automatic addressing is designed to serve the hosts in DMZ-sided and LAN-sided subnets. Hosts in WAN-sided subnets can only be addressed manually. DMZ-sided subnets are divided further into Subnet-in-DMZ, and Subnet-in-WAN-and-DMZ. FortiWAN’s automatic addressing is designed according to IPv4 network and IPv6 network, which is described as follows:
IPv4 Automatic addressing
FortiWAN provides standard DHCP and DHCP Relay to allocate IPv4 addresses to or relay DHCP messages for hosts in the following subnets or IP range:
| DMZ Side | l | Routing Mode, IPv4 Basic Subnet: Subnet in DMZ |
| l | Routing Mode, IPv4 Basic Subnet: Subnet in WAN and DMZ | |
| l | Bridge Mode: Multiple Static IP, IPv4 IP(s) in DMZ | |
| LAN Side | l | LAN Private Subnet |
DHCP
FortiWAN acts a DHCP server on the specified LAN port or DMZ port if checkbox Enable DHCP is checked. FortiWAN receives DHCP requests and responds related information from/to hosts (DHCP clients) in the subnets connect to the LAN or DMZ ports.
| Domain Name Server | The DNS that FortiWAN responds to the DHCP clients within the DHCP OFFER messages if the clients are sat to automatically get DNS information through DHCP. | |
| l | Single DNS server: the DNS servers defined in System > Network
Setting > DNS Server > IPv4 Domain Name Server are listed here for your options. |
|
| l | ALL: answer the DHCP clients with all the defined DNS servers information. | |
| l | None: answer the DHCP clients without containing any DNS server information.
This option is only available for LAN private subnet. For the DMZsided subnets (hosts in the two subnets are supposed to be deployed with public IP addresses), system behaves answering the DHCP clients with all the defined DNZ servers information. |
|
| Domain Name Suffix | The domain name suffix that FortiWAN responds to the DHCP clients within the DHCP OFFER messages if the clients are sat to automatically get DNS information from DHCP. | |
| l | Single domain name suffix: the domain name suffixes defined in System > Network Setting > DNS Server > Domain Name Suffix are listed here for your options. | |
| l | ALL: answer the DHCP clients with all the defined domain name suffixes. | |
| l | None: answer the DHCP clients without containing any domain name suffixes.
This option is only available for LAN private subnet. |
| TFTP Server Name | This option is used to deliver a TFTP server name to DHCP clients.
When the DHCP server see the request in a DHCP discover from a DHCP client, it returns the TFTP server name in its DHCP offer to the client as DHCP option 66. Usually, option 66 is used for IP phone auto-provisioning. You will need to refer to a vender’s documentation to configure this option. Specify the IP address or the hostname of a TFTP server directly here according to what the device vender provides. FortiWAN DHCP will directly return what is specified here to requests without any encoding/decoding. The DHCP server will ignore the request for option 66 from a DHCP client if this field is leaved blank. Note that FortiWAN does not support DHCP option 67 (Bootfile Name) and option 150 (TFTP Server Address). |
| Vendor Encapsulated Options | This option is used to transmit Vender Specific Information between the DHCP server and clients. Usually, the information could be the configuration data to the DHCP clients. For example an IP address of a WLAN controller or a DLS (Deployment Service) server, or an identifier if the DHCP clients are wireless APs, IP phones or other devices. When the DHCP server see the request in a DHCP discover (option 43 or number 43 included in option 55) from a DHCP client, it returns the vender specific information in its DHCP offer to the client as DHCP option 43.
The vender encapsulated option ca contain either a single venderspecific value or multiple vender-specific sub-options. The RFC allows a vender to define its own sub-option codes. All the suboptions are included in the DHCP offer as Type-Length-Value blocks embedded within the option 43. You will need to refer to a vender’s documentation to form the options to their specification. Specify the information directly here in hexadecimal numbering format according to what the device vender provides. FortiWAN DHCP will directly return what is specified here to requests without any encoding/decoding. The DHCP server will ignore the request for option 43 from a DHCP client if this field is leaved blank. Note that FortiWAN does not support DHCP option 60 (Vender Class Identifier), DHCP server will not return option 43 based on option 60. |
| DHCP Range | The address pools that DHCP server assigns and manages IP addresses from. Define the IP ranges by specifying IPv4 Starting Address and IPv4 Ending Address. |
| Static Mapping | DHCP server assigns and manages IP addresses according to clients’ MAC addresses. An IP address that is mapped to a MAC address is only available to the client with the MAC address. It will not be assigned to other client even it is idle. Define the mapping by specifying MAC Address and the correspondent IPv4 Address. |
| Client ID Mapping | DHCP server assigns and manages IP addresses according to the client ID of DHCP client (the Client Identifier, options code 61, in the options field of DHCP request). An IP address that is mapped to a client ID here is only available to this client. It will not be assigned to other clients even it is idle. Define the mapping by specifying Client ID and the correspondent IPv4 Address. Corresponding setting of client ID on a DHCP client is required. |
Note that IP addresses defined in DHCP Range, Static Mapping or Client ID Mapping must be also defined in filed IPv4 IP(s) in DMZ for a bridge-mode (multiple static IP) WAN link, the DMZ side of basic subnets (subnet in WAN and DMZ, and subnet in DMZ) for a routing-mode WAN link and the basic subnets of private LAN subnets.
DHCP Relay
DHCP relay is a proxy forwarding DHCP requests and responses between hosts and DHCP server across different subnets. A router called DHCP relay agent acts the proxy receiving DHCP requests from hosts in the same subnet and resending them to the DHCP server located in another subnet. The DHCP relay agent then delivers the DHCP messages responded by the DHCP server to the hosts in the subnet, so that the hosts are assigned the IP addresses and related information.
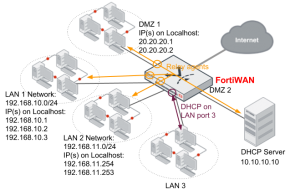
FortiWAN is the DHCP relay agent in the network once the DHCP Relay function is enable. Address allocation for multiple subnets (subnet in LAN, subnet in DMZ, subnet in WAN and DMZ and IPs in DMZ) can be managed by a centralized DHCP server. As the example below, FortiWAN relays the DHCP messages between the connected subnets and the standalone DHCP server, so that one DHCP server manages the address allocation for the three subnets, LAN 1, LAN 2 and a DMZ 1. As for subnet LAN 3, it employs FortiWAN’s DHCP server on LAN port 3. The enabled DHCP server on LAN port 3, which is independent from the standalone DHCP server, serves only subent LAN 3. Note that you can only enable either DHCP or DHCP Relay for a subnet.
To implement the deployment, you need to enable DHCP Relay for each of the subnets (enable DHCP Relay on each of the ports). In the example above, DHCP Relay is enabled on ports of LAN 1, LAN 2 and subnet in DMZ 1, and all the DHCP requests received on the ports will be forwarded to the DHCP server in the subnet DMZ 2. A LAN port or DMZ port with DHCP Relay being enabled on will forward the DHCP requests it received (coming from the subnet it connects to) to the DHCP server.
FortiWAN supports up to two DHCP servers in a DHCP relay deployment. Once two DHCP servers are configured, the relay agent will forward a DHCP request to both of the DHCP servers. The first response received by the relay agent will be first apply to the DHCP client, and the subsequent responses will be ignored then.
| DHCP Relay Server 1 | IP address of the first standalone DHCP server. | |
| DHCP Relay Server 2 | IP address of the second standalone DHCP server. Leave it blank if only one DHCP server is required for the DHCP relay deployment. | |
| DHCP Relay Agent IP | The IP address of the DHCP Relay agent on the port. It indicates the source of a relayed DHCP request to the DHCP server. This IP will be contained in a relayed DHCP message, so that the DHCP server could recognize the relay agent that the relayed DHCP request came from and respond the corresponding IP address to the DHCP client (according to this DHCP Relay Agent IP and the addressing policy).
The DHCP Relay Agent IP must be an IP address deployed on the localhost of the LAN port or DMZ port. You might deploy multiple IP addresses to a LAN port or a DMZ port (the field IP(s) on Localhost of a LAN subnet, a subnet in DMZ or a subnet in WAN and DMZ), then any of them could be took as the DHCP Relay Agent IP. |
|
Next are the configurations of DHCP Relay on the LAN 1, LAN 2 and DMZ ports in the example above.
LAN 1 subnet
From the example above, we have configured the localhost of LAN 2 port with three IP addresses 192.168.10.1, 192.168.10.2 and 192.168.10.3 for subnet 192.168.10.0/24. To enable DHCP Relay on this port, you need to check the check-box “Enable DHCP Relay” on the Web UI and configure the settings as follows:
| DHCP Relay Server 1 | 10.10.10.10 |
| DHCP Relay Agent IP | 192.168.10.1, 192.168.10.2 or 192.168.10.3 |
The DHCP server (10.10.10.10) recognizes the relay agent (the LAN 1 port) that relayed the DHCP message through the “DHCP Relay Agent IP” contained in the relayed message. Then according to the DHCP addressing policy, it selects an IP belongs to 192.168.10.x from its IP pool and responds to the relay agent on LAN 1 port.
LAN 2 subnet
From the example above, we have configured the localhost of LAN 1 port with three IP addresses
192.168.11.254 and 192.168.11.253 for subnet 192.168.11.0/24. To enable DHCP Relay on this port, you need to check the check-box “Enable DHCP Relay” on the Web UI and configure the settings as follows:
| DHCP Relay Server 1 | 10.10.10.10 |
| DHCP Relay Agent IP | 192.168.11.254 or 192.168.11.253 |
The DHCP server (10.10.10.10) recognizes the relay agent (the LAN 2 port) that relayed the DHCP message through the “DHCP Relay Agent IP” contained in the relayed message. Then according to the DHCP addressing policy, it selects an IP belongs to subnet 192.168.11.x from its IP pool and responds to the relay agent on LAN 2 port.
DMZ 1
As the previous description, DHCP relay agent enabled on a DMZ port forwards the DHCP messages between DMZ and a DHCP server. In FortiWAN, a DMZ can be deployed according the following WAN types:
l Routing Mode – IPv4 Basic Subnet: Subnet in DMZ l Routing Mode – IPv4 Basic Subnet: Subnet in WAN and DMZ l Bridge Mode – Multiple Static IP: IPv4 IP(s) in DMZ
No matter which WAN type a DMZ is deployed, it is necessary to configure the “IP(s) on Localhost” field to the DMZ port via Web UI. From the example above, we have configured the localhost of DMZ 1 port with three IP addresses 20.20.20.1 and 20.20.20.2. To enable DHCP Relay on this port, you need to check the check-box “Enable DHCP Relay” on the Web UI and configure the settings as follows:
| DHCP Relay Server 1 | 10.10.10.10 |
| DHCP Relay Agent IP | 20.20.20.1 or 20.20.20.2 |
The DHCP server (10.10.10.10) recognizes the relay agent (the DMZ 1 port) that relayed the DHCP message through the “DHCP Relay Agent IP” contained in the relayed message. Then according to the DHCP addressing policy, it selects an IP belongs to subnet 20.20.20.x from its IP pool and responds to the relay agent on DMZ 1 port.
Note that the DHCP server working with FortiWAN’s DHCP Replay must be a standalone server.
FortiWAN’s DHCP function is not supported to work with DHCP Relay; a port with DHCP being enabled can not cooperate with the ports that DHCP Relay is enabled on. The centralized DHCP server working in a DHCP Relay deployment must be well-configured in the IP pools for the multiple IP subnets it is managing.
DHCP Relay over FortiWAN Tunnel Routing network
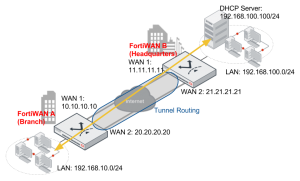
FortiWAN’s DHCP Relay is capable of forwarding DHCP messages through Tunnel Routing (See “Tunnel Routing”) so that the centralized IP addressing over a FortiWAN Tunnel Routing network can be implemented. This is useful for the application that a headquarters centrally manages IP allocation to its regional branches. The following shows the example that a DHCP server located in the headquarters site (deployed in the LAN subnet) manages the IP addressing to its branches through Internet.
With Tunnel Routing connectivity, a VPN network is established among networks of the two sites. DHCP relay in the VPN network serves for the subnets just as normal. FortiWAN A (the branch) delivers the relayed DHCP requests from its private subnet 192.168.10.0/24 to the DHCP server located in remote private subnet 192.168.100.0/24 over Internet; conversely, FortiWAN B (the headquarters) delivers the DHCP responses to the branch site over Internet and FortiWAN A will forward the response to its LAN to allocate a host the IP address. DHCP messages are delivered by Tunnel Routing encapsulation and decapsulation, just like normal Tunnel
Routing transmission. The localhost of LAN port on FortWAN A is configured to 192.168.10.254. Configuration of IP pool for subnet 192.168.10.0/24 is required on the DHCP server. The related configurations on the two FortiWAN units are as follows:
Configurations on FortiWAN A
Go to Network Setting > LAN Private Subnet > IPv4 Basic Subnetand select the subnet 192.168.10.0/24 to configure.
Check the checkbox Enable DHCP Relay and configure the setting below.
| DHCP Relay Server 1 | 192.168.100.100 |
| DHCP Relay Agent IP | 192.168.10.254 |
Go to Service > Tunnel Routing and define a Tunnel Group with the two tunnels below:
| Local IP | Remote IP |
| 10.10.10.10 | 11.11.11.11 |
| 20.20.20.20 | 21.21.21.21 |
Define the Routing Rule.
| Source | Destination | Service | Group |
| 192.168.10.0/255.255.255.0 | 192.168.100.0/255.255.255.0 | Any | Group Name |
Configurations on FortiWAN B
Go to Service > Tunnel Routing and define a Tunnel Group with the two tunnels below:
| Local IP | Remote IP |
| 11.11.11.11 | 10.10.10.10 |
| 21.21.21.21 | 20.20.20.20 |
Define the Routing Rule.
| Source | Destination | Service | Group |
| 192.168.100.0/255.255.255.0 | 192.168.10.0/255.255.255.0 | Any | Group Name |
Note that the DHCP Relay can only work with Tunnel Routing or Tunnel Routing over IPSec Transport Mode. It does not support relaying DHCP requests through IPSec Tunnel Mode (See “IPSec VPN”).
IPv6 Automatic Addressing
FortiWAN provides stateless and stateful mechanisms to allocate IPv6 addresses to hosts in the following subnets or IP range:
| DMZ Side | l | Routing Mode, IPv6 Basic Subnet: Subnet in DMZ |
| l | Routing Mode, IPv6 Basic Subnet: Subnet in WAN and DMZ | |
| l | Bridge Mode: One Static IP, IPv6 Basic Subnet: Subnet in DMZ | |
| l | Bridge Mode: Multiple Static IP, IPv6 IP(s) in DMZ | |
| l | Bridge Mode: Multiple Static IP, IPv6 Basic Subnet: Subnet in DMZ | |
| LAN Side | l | LAN Private Subnet |
Stateless Address Autoconfiguration (SLAAC) is a standard mechanism to equip hosts with IPv6 addresses and related routing information through the IPv6 router advertisements (RA). SLAAC has two properties:
- SLAAC is a stateless mechanism which is short of the IP management. SLAAC is incapable of controlling the
mapping between a host and an IPv6 address.
- DNS information is absent from the traditional Router Advertisement messages. SLAAC with options of RDNSS and DNSSL included in RA messages (what is called SLAAC RDNSS) can convey information about DNS recursive servers and DNS Search Lists.
Comparing with SLAAC, DHCPv6 takes the advantage of IP management, so that is called stateful. By specifying the IP pool and static IP mapping, administrators are able to control how the IPv6 addresses be allocated via DHCPv6. FortiWAN provides both SLAAC RDNSS and DHCPv6 for the stateless and stateful IPv6 automatic addressing
Stateless IPv6 addressing: SLAAC
Enabling the stateless IPv6 addressing for the “IPv6 Basic Subnets” or “IPv6 (IPs) in DMZ” by checking the checkbox Enable SLAAC.
| DNS Server | The recursive DNS servers used to serve the IPv6 subnet you are configuring (the Subnet field below). FortiWAN conveys it through router advertisement (RA) messages. Depending on the subnet type (DMZ-sided or LAN-sided), this could be the DNS server serving the global IPv6 subnets (public) that your ISP provides or the
DNS server for the unique local IPv6 subnet (private). |
|
| l | Single DNS server: the IPv6 addresses defined in System > Network
Setting > DNS Server > IPv6 Domain Name Server are listed here for your options |
|
| l | ALL: answer the hosts with all the defined IPv6 DNS servers information. | |
| l | None: answer the hosts without containing any IPv6 DNS server information.
This option is only available for IPv6 LAN private subnet. For the DMZ-sided subnets (hosts in the subnets are supposed to be deployed with IPv6 global addresses), system behaves answering the hosts with all the defined DNZ servers information. |
|
| Subnet | The subnet deployed on the port (LAN port or DMZ port) you are configuring. SLAAC services the subnet. The subnet is used by SLAAC to allocate the prefix information to the hosts, so that an IPv6 address can be determined (with the Host ID) on a host. Depending on the subnet type, it could be a global IPv6 subnet or a unique local IPv6 subnet. | |
| DNS Search List | A search list to be used when trying to resolve a name by means of the DNS. This option is only available for IPv6 LAN private subnet. |
Stateful IPv6 addressing: DHCPv6
To enable the stateful IPv6 addressing for the “IPv6 Basic Subnets” or “IPv6 (IPs) in DMZ”, you are required to enable and configure both SLAAC and DHCPv6 on Web UI. FortiWAN will not respond for any Router
Advertisement (RA) if it SLAAC is disabled. The stateful IPv6 addressing via DHCPv6 requires RA to discover the default gateway for hosts, and therefor hosts fail to get default gateway if SLAAC is disabled. Please enable and configure the SLAAC as the introduction above if DHCPv6 is enable and make sure the network interface of a host is sat to automatically get the IPv6 address through DHCPv6.
FortiWAN acts a DHCPv6 server on the specified LAN port or DMZ port if checkbox Enable DHCPv6 Service is checked. All the hosts running as DHCPv6 client could gain the routing and DNS information from DHCPv6 server. DHCPv6 provides configuring and management to the IPv6 addresses to be assigned, which is a shortage of SLAAC.
| DNS Server | The DNS DNS servers used to serve the IPv6 subnet you are configuring (the Subnet field below). FortiWAN responds to the DHCPv6 clients within the DHCPv6 messages if the clients are sat to automatically get DNS information through DHCPv6. Depending on the subnet type (DMZ-sided or LAN-sided), this could be the DNS server serving the global IPv6 subnets (public) that your ISP provides or the DNS server for the unique local IPv6 subnet
(private). |
|
| l | Single DNS server: the IPv6 addresses defined in System > Network Setting > DNS Server > IPv6 Domain Name Server are listed here for your options. | |
| l | ALL: answer the hosts with all the defined IPv6 DNS servers information. | |
| l | None: answer the hosts without containing any IPv6 DNS server information.
This option is only available for IPv6 LAN private subnet. For subnet in DMZ and subnet in WAN and DMZ (hosts in the subnets are supposed to be IPv6 global address deployment), system behaves answering the hosts with all the defined DNZ servers information. |
|
| DHCP Range | The address pools that DHCPv6 server assigns and manages IPv6 addresses from. Define the DHCP ranges by specifying IPv6 Starting Address and IPv6 Ending Address. | |
| Static Mapping | DHCPv6 server assigns and manages IPv6 addresses according to client IDs. An IPv6 address that is mapped to a client ID is only available to this client. It will not be assigned to other clients even it is idle. Define the mapping by specifying Client ID and the correspondent IPv6 Address. | |
| DNS Search List | A search list to be used when trying to resolve a name by means of the DNS. This option is only available for IPv6 LAN private subnet. |
Note that IPv6 addresses defined in DHCP Range and Static Mapping must be also defined in filed IPv6 IP(s) in DMZ for a bridge-mode (multiple static IP) WAN link, the DMZ side of IPv6 basic subnets (subnet in WAN and DMZ, and subnet in DMZ) for a routing-mode WAN link and the IPv6 basic subnets of private LAN subnets.

BTW, do you know how if FortiGate is able to provide RDNSS support and how to configure it in an interface?. Thanks
FortiGate DNS server capabilities are extremely rudimentary. I know the FortiWAN can do RDNSS but I have never tried or experienced it with the Gate.