Deployment Scenarios for Various WAN Types
This Section provides various network scenarios for the different WAN types and explains how FortiWAN can easily be integrated into any existing networks.
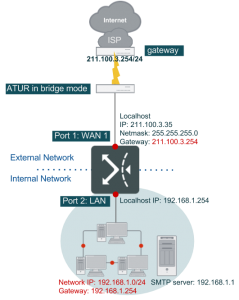
WAN Type: Bridge Mode with a Single Static IP
Single Static IP is a common and simple WAN network scenario, where the ISP provides a single public static (fixed) IP for the WAN link. Note: ISP often provides ATU-R, sometimes known as ADSL Modems with bridge model.
In this example it is assumed that WAN port 1 is connected to the bridge-mode ATU-R.
Please refer to the ATU-R User manual provided by your ISP to connect the ATU-R to FortiWAN’s WAN #1. Connect LAN to FortiWAN’s LAN port via a switch or hub. In this example, FortiWAN’s Port2 is treated as LAN port. Please map FortiWAN’s LAN port to the Port2 in [System] → [Network Setting] → [VLAN and Port Mapping]. Note: FortiWAN is treated as a normal PC when connecting to other networking equipments.
WAN configuration:
- Enter FortiWAN’s Web-based UI.
- Go to [System] → [Network Setting] → [WAN Settings].
- In the WAN LINK scroll menu, select “1”, and choose “Enable” in the Basic Settings.
- In the WAN type scroll menu, select [Bridge Mode: One static IP].
- Select [Port 1] in the WAN Port field.
- Enter the up/down stream bandwidth associated with this WAN link. Example: If the ADSL Line on WAN1 is 512/64, then enter [64] and [512] in the Up Stream and Down Stream fields respectively. Note: The up/down stream values entered will ONLY affect the BM and statistics reporting. Bandwidth will not increase if the values are greater than the actual bandwidth.
- Enter [211.100.3.35] in the Localhost IP field.
- Enter [255.255.255.0] in the Netmask field.
- Enter [211.100.3.254] in the Default Gateway IP field.
- Apply the bridge mode configuration.
- If the configuration above has been correctly established, in the [System] →[Summary] page, the status color on the WAN Link State for WAN Link #1 will turn green.
LAN configuration:
- Go to [System] → [Network Setting] → [LAN Private Subnet].
- Enter [192.168.1.254] in the IP(s) on Localhost field.
- Enter [255.255.255.0] in the Netmask field.
- Select [Port2] in the LAN Port field.
- Check NAT Subnet for VS.
- Configuration complete.
Virtual Server Configuration:
Assume an SMTP server with IP 192.168.1.1 provides SMTP services to the outside via the virtual server. FortiWAN will perform NAT on this machine so that the outside clients can get SMTP services via FortiWAN’s public IP on WAN1. The settings for this are in [Service] → [Virtual Server].
- Click [+] to create a new rule.
- Check [E] to enable this rule.
- Select [All-Time] in the “When” field.
- Enter [211.100.3.35] in the WAN IP field.
- Select [SMTP(25)] in the Service field.
- Select [Round-Robin] in the Algorithm field.
- Click [+] to create a new server in Server Pool.
- Enter [192.168.1.1] in the Server IP field.
- Select [SMTP(25)] in the Service field.
- Enter [1] in the Weight field.
- Selection of the L field is optional. (If an Administrator wishes to log Virtual Server activities, please select “L”).
- Configuration complete.
Administrators can set up different types of services inside the LAN and use the Virtual Server to make these services available to public once the configurations are completed.