Antivirus concepts
The word “antivirus” refers to a group of features that are designed to prevent unwanted and potentially malicious files from entering your network. These features all work in different ways, which include checking for a file size, name, or type, or for the presence of a virus or grayware signature.
The antivirus scanning routines your FortiGate unit uses are designed to share access to the network traffic. This way, each individual feature does not have to examine the network traffic as a separate operation, and the overhead is reduced significantly. For example, if you enable file filtering and virus scanning, the resources used to complete these tasks are only slightly greater than enabling virus scanning alone. Two features do not require twice the resources.
Antivirus scanning examines files for viruses, worms, trojans, and other malware. The antivirus scan engine has a database of virus signatures it uses to identify infections. If the scanner finds a signature in a file, it determines that the file is infected and takes the appropriate action.
Malware Threats
Viruses
Viruses are self replicating code that install copies of themselves into other programs, data files for boot sectors of storage devices. Virus can often carry a “payload” which performs some undesirable function. These functions can include but are not limited to:
- Stealing drive space
- Stealing cpu cycles
- Accessing private information
- Corrupting data
- Digital defacement or vandalism
- Spamming contact lists
Worms
A worm is a piece of standalone computer code that replicates itself in order to spread to other computers. It normally uses a computer network to spread itself, using security vulnerabilities on the target computer or network to propagate. Unlike a virus, it does not attach itself to an existing file. Even is there is no payload, worms consume resources such as bandwidth and storage space just through their act of replication.
Trojan horses
A Trojan horse, or Trojan is malware that is defined by its delivery method. Through the use of social engineering, or some other method, the code is installed on a system by a valid user of the system and like the original Trojan horse there is something more than advertised within the software. Trojans, unlike worms or viruses are generally non-self-replicating. The most common payload of a Trojan is the setting up of a “backdoor” control mechanism to the system that it is installed on.
Ransomware
Ransomware is a type of malware that, as the name implies, hold the system ransom until payment of some kind is made. It does this by restricting access to the legitimate owner of the system either by encrypting files or locking the system. Usually, a message of some kind is displayed with the demands. Upon payment a utility or key is sent to the user to unlock the system.
Scareware
Scareware comes in two main flavours; the first tries to convince the user that his computer is invected with some non-existent malware, scaring the user into purchasing the author’s virus removal utility. The utility is nonfunctional or some additional form of malware.
The second form tries to convince the user that the computer has been or is being used for an illegal act such as being part of a bot net or storing child pornography. Again, the objective is to scare the user into paying to cure something that is not really there.
Spyware
Spyware is used by its authors to collect information about the user and its computer without the users knowledge. The end result can be as benign as being better able to target adds, to as criminal as key loggers designed to record account ids and passwords of bank accounts and forward them off to the authors.
Adware
Adware is not malware per se. It is merely any software that produces advertisements in order to generate revenue for its author. While a lot of people find this inconvenient or irritating it is not malware. As such it is not blocked by the antivirus software for being malware. This doesn’t mean that software that has adware built into it will not be block if it does have malware in it.
Botnets
A botnet is a network of Internet connected computers that have been covertly usurped to forward transmissions to other computers on the Internet on behalf of a “master”. These transmission can be merely annoying such as spam or they can critically impact a target as when used to launch a Distributed Denial of Service attack.
Any such computer is referred to as a zombie – in effect, a computer “robot” or “bot” that serves the wishes of some master spam or virus originator. Most computers compromised in this way are home-based.
According to a report from Russian-based Kaspersky Labs, botnets — not spam, viruses, or worms — currently pose the biggest threat to the Internet. A report from Symantec came to a similar conclusion.
Phishing
Phishing is a social engineering technique that is used to obtain sensitive and confidential information by masquerading as a communication from a trusted entity such as a well known institution, company, or website. Usually, the malware is not in the communication itself but in the links within the communication.
Grayware
Grayware programs are unsolicited software programs installed on computers, often without the user’s consent or knowledge. Grayware programs are generally considered an annoyance, but they can also cause system performance problems or be used for malicious purposes.
Scanning Modes
FortiOS has two different mode of scanning for malware. The reasons for the different modes are performance and granularity. In just about everything relating to security there is a constant balancing act going on. As you increase the level of security and comprehensiveness, there is by necessity a decrease in either convenience or performance, sometimes both. The increase in processing to scan for more threats requires more resources; resources that are a finite supply on the hardware. Granularity can sometimes be used to mitigate performance impact by scanning for a smaller subset of traffic but this is only recommended when that smaller subset of traffic is the only traffic going through the firewall.
If the traffic on the device is slight then the impact on the performance will hardly be noticeable, but it the unit is working close to capacity in terms of traffic and there are a lot of files coming through then there might be a noticeable decline in the performance.
While both modes offer significant security, Proxy-based is weighted towards being more thorough and easily configurable, while Flow-based is designed to optimize performance.
Proxy
The most thorough scan requires that the FortiGate unit have the whole file for the scanning procedure. To achieve this, the antivirus proxy buffers the file as it arrives. Once the transmission is complete, the virus scanner examines the file. If no infection is present, it is sent to the destination. If an infection is present, a replacement message is set to the destination.
During the buffering and scanning procedure, the client must wait. With a default configuration, the file is released to the client only after it is scanned. You can enable client comforting in the Proxy Options profile to feed the client a trickle of data to prevent them from thinking the transfer is stalled, and possibly cancelling the download.
Buffering the entire file allows the FortiGate unit to eliminate the danger of missing an infection due to fragmentation because the file is reassembled before examination. Archives can also be expanded and the contents scanned, even if archives are nested.
Since the FortiGate unit has a limited amount of memory, files larger than a certain size do not fit within the memory buffer. The default buffer size is 10 MB. You can use the uncompsizelimit CLI command to adjust the size of this memory buffer.
Files larger than the buffer are passed to the destination without scanning. You can use the Oversize File/Email setting to block files larger than the antivirus buffer if allowing files that are too large to be scanned is an unacceptable security risk.
Flow–based
If your FortiGate unit supports flow-based antivirus scanning, you can select it instead of proxy-based antivirus scanning. The way flow-based antivirus works changed significantly starting with firmware version 5.2.
As packets of a file come into the FortiGate unit, a copy of the packet is cached locally before the packet is allowed to pass through to the recipient. When the last packet of the file arrives, it is also cached but put on hold. Now the entire cached file is delivered to the Antivirus engine for a full scanning, just as it would be if using the proxy-based method, using what ever antivirus database has been configured.
If the file is determined to be infected with malware, the last packet will be dropped and the session is reset. Without all of the packets the file cannot be built by the recipient. When download a file through an HTTP connection (or HTTPS is SSL scanning is enabled), the flow-based feature remembers the last virus result so any subsequent attempts to download the same file will be welcomed by an appropriate blocked message directly, without engaging in the effort of downloading the file.
By using the same engine as the proxy-based method the detection rate is the same for both methods. In terms of performance from the end user’s stand point, the performance of the download will be a lot faster until the last packet and then there will be a slight delay for the scan, but after the determination is made only one packet has to be sent from the firewall to the recipient so the overall speed is faster than the proxy based method.
Another advantage of the flow-based method is that the scanning process does not change the packets as they pass through the FortiGate unit, while proxy-based scanning can change packet details such as sequence numbers. The changes made by proxy-based scanning do not affect most networks.
Additionally, when configuring flow-based virus scanning you can now choose between Quick and Full scan mode. Full mode is the same as flow-based scanning in FortiOS 5.2. Quick mode uses a compact antivirus database and advanced techniques to improve performance. Use the following command to enable quick or full mode in an antivirus profile:
config antivirus profile edit <profile>
set scan-mode [quick | full]
end
Antivirus scanning order
The antivirus scanning function includes various modules and engines that perform separate tasks.
Proxy–based antivirus scanning order
The following figure illustrates the antivirus scanning order when using proxy-based scanning. The first check for oversized files/email is to determine whether the file exceeds the configured size threshold. The uncompsizelimit check is to determine if the file can be buffered for file type and antivirus scanning. If the file is too large for the buffer, it is allowed to pass without being scanned. For more information, see the config antivirus service command. The antivirus scan includes scanning for viruses, as well as for grayware and heuristics if they are enabled.
File filtering includes file pattern and file type scans which are applied at different stages in the antivirus process.
Antivirus scanning order when using the normal, extended, or extreme database
If a file fails any of the tasks of the antivirus scan, no further scans are performed. For example, if the file fakefile.EXE is recognized as a blocked file pattern, the FortiGate unit will send the end user a replacement message, and delete or quarantine the file. The unit will not perform virus scan, grayware, heuristics, and file type scans because the previous checks have already determined that the file is a threat and have dealt with it.
Flow–based antivirus scanning order
The following figure illustrates the antivirus scanning order when using flow-based scanning (i.e. the flow-based database). The antivirus scan takes place before any other antivirus-related scan. If file filter is not enabled, the file is not buffered. The antivirus scan includes scanning for viruses, as well as for grayware and heuristics if they are enabled.
Start
FTP, NNTP, SMTP,
POP3, IMAP, HTTP traffic
Scanning stage
Antivirus profile filtering stage
Buffering stage
File message is buffered
Yes
Oversized threshold checking stage
Pattern matching stage
Uncompsizelimit threshold checking stage
Type matching stage
Block
Pass file/ email
Passes to next process
Antivirus databases
The antivirus scanning engine relies on a database of virus signatures to detail the unique attributes of each infection. The antivirus scan searches for these signatures, and when one is discovered, the FortiGate unit determines the file is infected and takes action.
All FortiGate units have the normal antivirus signature database but some models have additional databases you can select for use. Which you choose depends on your network and security needs.
Normal Includes viruses currently spreading as determined by the FortiGuard Global Security Research Team. These viruses are the greatest threat. The Normal database is the default selection and it is available on every FortiGate unit.
Extended Includes the normal database in addition to recent viruses that are no-longer active. These viruses may have been spreading within the last year but have since nearly or completely disappeared.
Extreme Includes the extended database in addition to a large collection of ‘zoo’ viruses. These are viruses that have not spread in a long time and are largely dormant today. Some zoo viruses may rely on operating systems and hardware that are no longer widely used.
If your FortiGate unit supports extended, extreme, or flow-based virus database definitions, you can select the virus database most suited to your needs.
If you require the most comprehensive antivirus protection, enable the extended virus database. The additional coverage comes at a cost, however, because the extra processing requires additional resources.
To change the antivirus database
Use the CLI to run the following commands:
config antivirus settings set default-db extended
end
Antivirus techniques
The first three antivirus features work in sequence to efficiently scan incoming files and offer your network optimum antivirus protection. The first two features have specific functions, the third, heuristics, protects against new, or previously unknown virus threats.
To ensure that your system is providing the most protection available, all virus definitions and signatures are updated regularly through the FortiGuard antivirus services. These updates can be scheduled as often as on an hourly basis. To configure this feature, go to System > FortiGuard. Under AntiVirus & IPS Scanning, enable Schedule Updates. From here you can set the updates to occur on a consistent weekly, daily, or even hourly basis.
Virus scan
If the file passes the file pattern scan, the FortiGate unit applies a virus scan to it. The virus definitions are kept up-to-date through the FortiGuard Distribution Network (FDN).
Grayware protection
If the file passes the virus scan, it can be checked for grayware.
Grayware scanning is an optional function and must be enabled in the CLI if it is to be scanned for along with other malware. Grayware cannot be scanned for on its own. While done as a separate step, antivirus scanning must be enabled as well.
To enable grayware detection enter the following in the CLI:
config antivirus settings set grayware enable
end
To disable grayware detection enter the following in the CLI:
config antivirus settings set grayware disable
end
Grayware signatures are kept up to date in the same manner as the antivirus definitions.
Heuristics
After an incoming file has passed the grayware scan, it is subjected to the heuristics scan. The FortiGate heuristic antivirus engine, if enabled, performs tests on the file to detect virus-like behavior or known virus indicators. In this way, heuristic scanning may detect new viruses, but may also produce some false positive results. You configure heuristics from the CLI.
To set heuristics, enter the following in the CLI:
config antivirus heuristic
set mode {pass |block |disable}
end
- “block” enables heuristics and any files determined to be malware are blocked from entering the network.
- “pass” enables heuristics but any files determined to be malware are still allowed to pass through to the recipient.
- “disable” turns off heuristics.
FortiGuard Antivirus
The FortiGuard Antivirus services are included in the regular FortiGuard subscription and include automatic updates of antivirus engines and definitions as well as a DNS black list (DNSBL) through the FortiGuard Distribution Network (FDN).
Current information about your subscription and version numbers can be found at System > FortiGuard. This page will also allow the configuration of connections to the FortiGuard Center and how often to check for updates to the antivirus files.
FortiGuard Botnet protection
Protection from having your system being controlled by a botnet is achieved by detecting and blocking connection attempts to known botnets. This feature also includes connections to known phishing sites. The FortiGuard database includes a constantly updated database of known Command and Control (C&C) sites that Botnet clients attempt to connect to, as well as a database of phishing URLs.
To enable Botnet and phishing protection in a DNS Filter profile, enable Block DNS requests to known botnet C&C.
The latest Botnet database is available from FortiGuard. To see the version of the database and display its contents, go to System > FortiGuard > Botnet Definitions. You can also block, monitor, or allow outgoing connections to Botnet sites for each FortiGate interface.
Both the DNS Filter security profile and Botnet protection feature are only available for proxy-based inspection.
Quarantine / Source IP ban
As of FortiOS 5.2, quarantine was a place where traffic content was held in storage where it couldn’t interact with the network or system. This was removed, but the term quarantine was kept to describe keeping selected source IPs from interacting with the network and protected systems. This source IP ban is kept in the kernel rather than in any specific application engine and can be queried by APIs. The features that can use the APIs to access and use the banned source IP addresses are antivirus, DLP, DoS and IPS. Both IPv4 and IPv6 version are included in this feature.
To configure the antivirus profile to add the source IP address of an infected file to the quarantine or list of banned source IP addresses edit the Antivirus profile, in the CLI as follows:
config antivirus profile edit <name of profile>
config nac-quar
set infected quar-src-ip set expiry 5m
end
If the quar-src-ip action is used, the additional variable of expiry time will become available. This variable determines for how long the source IP adddress will be blocked. In the CLI the option is called expiry and the duration is in the format <###d##h##m>. The maximum days value is 364. The maximum hour value is 23 and the maximum minute value is 59. The default is 5 minutes.
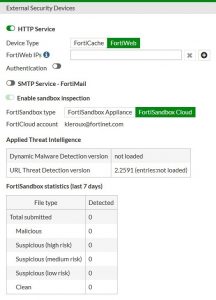
FortiSandbox
Not every piece of malware has a signature yet. This is especially true of new malware and new variations on existing malware. FortiOS can upload suspicious files to FortiSandbox where the file will be executed and the resulting behavior analyzed for risk. If the file exhibits risky behavior or is found to contain a virus, a new virus signature is created and added to the FortiGuard antivirus signature database. The next time your FortiGate unit updates its antivirus database it will have the new signature.
A file is considered suspicious if it does not contain a known virus and if it has some suspicious characteristics. The suspicious characteristics can change depending on the current threat climate and other factors. Fortinet optimizes how files are uploaded as required.
To configure an Antivirus profile to enable the use of the FortiSandbox check the checkbox next to Send Files to FortiSandbox Cloud for Inspection — this requires you have a FortiCloud account active.
Sending files to the FortiSandbox Cloud does not block files that it uploads. Instead they are used to improve how quickly new threats can be discovered and signatures created for them and added to the FortiGuard antivirus database.
The Advanced Threat Protection dashboard widget shows the number of files that your FortiGate unit has uploaded or submitted to FortiSandbox. To see more information regarding the version of the database and display its contents, go to System > External Security Devices.
Client Comforting
When proxy-based antivirus scanning is enabled, the FortiGate unit buffers files as they are downloaded. Once the entire file is captured, the FortiGate unit scans it. If no infection is found, the file is sent along to the client. The client initiates the file transfer and nothing happens until the FortiGate finds the file clean, and releases it. Users can be impatient, and if the file is large or the download slow, they may cancel the download, not realizing that the transfer is in progress.
The client comforting feature solves this problem by allowing a trickle of data to flow to the client so they can see the file is being transferred. The default client comforting transfer rate sends one byte of data to the client every ten seconds. This slow transfer continues while the FortiGate unit buffers the file and scans it. If the file is infection-free, it is released and the client will receive the remainder of the transfer at full speed. If the file is infected, the FortiGate unit caches the URL and drops the connection. The client does not receive any notification of what happened because the download to the client had already started. Instead, the download stops and the user is left with a partially downloaded file.
If the user tries to download the same file again within a short period of time, the cached URL is matched and the download is blocked. The client receives the Infection cache message replacement message as a notification that the download has been blocked. The number of URLs in the cache is limited by the size of the cache.
Client comforting can send unscanned and therefore potentially infected content to the client. You should only enable client comforting if you are prepared to accept this risk. Keeping the client comforting interval high and the amount low will reduce the amount of potentially infected data that is downloaded.
Client comforting is available for HTTP and FTP traffic. If your FortiGate unit supports SSL content scanning and inspection, you can also configure client comforting for HTTPS and FTPS traffic.
Enable and configure client comforting
1. Go to Security Profiles > Proxy Options.
2. Select a Proxy Options profile and choose Edit, or select Create New to make a new one.
3. Scroll down to the Common Options section and check the box next to Comfort Clients. This will set the option on all of the applicable protocols. The ability to set this feature on a protocol by protocol basis exists in the CLI
4. Select OK or Apply to save the changes.
5. Select this Proxy Options profile in any security policy for it to take effect on all traffic handled by the policy. The default values for Interval and Amount are 10 and 1, respectively. This means that when client comforting takes effect, 1 byte of the file is sent to the client every 10 seconds. You can change these values to vary the amount and frequency of the data transferred by client comforting.
Oversized files and emails
Downloaded files can range from a few Kilobytes to multiple Gigabytes. The problem lies in that a FortiGate doesn’t have the memory to allow for a large number of people downloading large files. Image the memory required for a team of developers to all download the latest Linux OS distribution at once, in addition to the normal requirements of the firewall. Everything would come to a grinding halt the FortiGate tried to store each of those Gibabyte+ files in memory. To give you some piece of mind, the chances of malware being in a large file like those is much smaller than in a smaller single Megabyte file, so the threat is somewhat limited, but you will probably want to use your computers antivirus software to scan those large files after they have been downloaded.
Therefore a threshold must be set to prevent the resources of the system from becoming overloaded. By default the threshold is 10 MB. Any files larger than the threshold will not be scanned for malware. With a maximum file size threshold in place, it must now be determined what is to be done with the files that are larger than threshold. There are only 2 choices; either the file is passed through without being scanned for malware or the file is blocked. The default action for oversized files is to pass them through.
If you wish to block the downloading of files over the threshold, this can be set within the Proxy Option profile found at Security Profiles > Proxy Options, under Common Options.
Check Block Oversized File/Email.
This will reveal an additional option, Threshold (MB). The threshold of the files is set based upon the protocol being used to transfer the file. In the CLI and configuration file, the threshold variable is found in each of the protocol sections within the profile. Changing the value in this field will change the oversize-limit value for all of the protocols.
If you wish to change the oversize-limit value on all of the protocols covered in a Proxy Option profile you have two options.
1. You can go into the CLI and change the value manually within each of the protocol sections.
2. You can use the GUI to temporarily block oversized files, and when configuring it change the threshold to the new value that you want. Apply this setting. Then go back to the profile and turn off the block setting. If you now go into the CLI you will find that the configuration file has retained the new oversize-limit value.
The settings can be found in the CLI by going to:
config firewall profile-protocol-options edit <the name of the profile>
Archive scan depth
The antivirus scanner will open archives and scan the files inside. Archives within other archives, or nested archives, are also scanned to a default depth of twelve nestings. You can adjust the number of nested archives to which the FortiGate unit will scan with the uncompressed-nest-limit CLI command. Further, the limit is configured separately for each traffic type.
Configuring archive scan depth
For example, this CLI command sets the archive scan depth for SMTP traffic to 5. That is, archives within archives will be scanned five levels deep.
config firewall profile-protocol-options
edit “default” config http
set uncompressed-nest-limit 5 end
You can set the nesting limit from 2 to 100.
Scan buffer size
When checking files for viruses, there is a maximum file size that can be buffered. Files larger than this size are passed without scanning. The default size for all FortiGate models is 10 megabytes.
Archived files are extracted and email attachments are decoded before the FortiGate unit determines if they can fit in the scan buffer. For example, a 7 megabyte ZIP file containing a 12 megabyte EXE file will be passed without scanning with the default buffer size. Although the archive would fit within the buffer, the uncompressed file size will not.
Configuring the uncompression buffer
In this example, the uncompressed-oversize-limit CLI command is used to change the scan buffer size to 20 megabytes for files found in HTTP traffic:
config firewall profile-protocol-options
edit “default” config http
set uncompressed-oversize-limit 20 end
The maximum buffer size varies by model. Enter set uncompressed-oversize-limit ? to display the buffer size range for your FortiGate unit.
Windows file sharing (CIFS)
FortiOS supports virus scanning of Windows file sharing traffic. This includes CIFS, SMB, and SAMBA traffic. This feature is applied by enabling SMB scanning in an antivirus profile and then adding this profile to a security policy that accepts CIFS traffic. CIFS virus scanning is available only through flow-based antivirus scanning.
FortiOS flow-based virus scanning can detect the same number of viruses in CIFS/SMB/SAMBA traffic as it can for all supported content protocols.
Note the following about CFIS/SMB/SAMBA virus scanning:
- Some newer version of SAMBA clients and SMB2 can spread one file across multiple sessions, preventing some viruses from being detected if this occurs.
- Enabling CIFS/SMB/SAMBA virus scanning can affect FortiGate performance.
- SMB2 is a new version of SMB that was first partially implemented in Windows Vista.
- Currently SMB2 is supported by Windows Vista or later, and partly supported by Samba 3.5 and fully support by Samba 3.6.
- The latest version of SMB2.2 will be introduced with Windows 8.
- Most clients still use SMB as default setting.
Configuring CIFS/SMB/SAMBA virus scanning
Use the following command to enable CIFS/SMB/SAMBA virus scanning in an antivirus profile:
config antivirus profile edit <smb-profile>
config smb
set options scan end
Then add this antivirus profile to a security policy that accepts the traffic to be virus scanned. In the security policy the service can be set to ANY, SAMBA, or SMB.
config firewall policy edit 0
set service ANY
…
set utm-status enable
set av-profile <smb-profile>
end