Configuring networks to FortiWAN
As the previous description, FortiWAN is an intelligent WAN load balancing device providing services to increase connection efficiency and reliability between the internal and external networks, but basically as an router it is fundamental to route IP packets among the connected networks. According to different purpose and functionality, a connected network could be one of the three types: WAN, LAN and DMZ networks. When you configure setting of a network to a FortiWAN, you are registering the network to the FortiWAN (majorly adding related routing information about the network to the FortiWAN), so that the FortiWAN can find the path to correctly route packets destined to the network. Network settings establish the necessary routing rules to FortiWAN so that the connected WAN, LAN and DMZ networks can communicate to each other. Besides setting routing rules, network setting requires other necessary information used to guarantee a well-cooperation between the connected network and FortiWAN. No matter what types those connected networks are, there are some common concepts among the settings:
Static route: basic subnets & static routing subnets
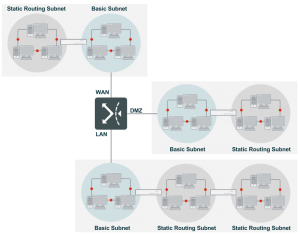
Within a network site, FortiWAN routes communication among the connected WAN (near WAN actually, see WAN, LAN and DMZ and Near WAN), LAN and DMZ networks according to established static routing entries, without WAN load balancing and fail-over being involved. Those static routing entries of connected networks are manually added to FortiWAN by network settings. A connected network can contain several subnets. Basically, FortiWAN defines two types of subnets to a connected network for it static route, basic subnet and static routing subnet:
Basic subnet: Any subnet connected directly to FortiWAN’s network port is called a basic subnet. Setting for a basic subnet tells FortiWAN the network IP, netmask of the subnet and the connected port, so that FortiWAN is aware of the network port used to directly deliver the packets destined to the subnet.
Static routing subnet: Any subnet connected directly or indirectly to a FortiWAN’s basic subnet is called a static routing subnet. Setting for a static routing subnet tells FortiWAN the network IP, netmask of the subnet and the gateway, so that FortiWAN can fine the next hop to forward packets destined to the subnet, although the static routing subnet does not connect directly to the FortiWAN.
Basically, all the network configurations in WAN Setting (see Configuring your WAN and DMZ), WAN/DMZ Private Subnet (see WAN/DMZ Private Subnet) and LAN Private Subnet (see LAN Private Subnet) contain settings of basic subnet and static routing subnet, except IPv4-based bridge-mode WAN links. FortiWAN’s basic subnets and static routing subnets are static routes, therefore, any physical change to deployment of the subnets requires corresponding modifications to the routing entries. The basic static route is supposed to be suitable for simple topologies. When you have a large-scale network with complex topologies, dynamic routing would be much suitable for it. FortiWAN supports RIP (v1 and v2), OSPF and VRRP on its LAN ports.
IPv4/IPv6 dual stack
FortiWAN supports IPv4/IPv6 dual stack, which means a FortiWAN can be configured with both IPv4 and IPv6 connectivity capabilities (FortiWAN does not support a pure IPv6 based network). None of IPv4 network and IPv6 network is dispensable for configuring a dual stack network to FortiWAN. Therefore, the required static routing information for configuring a dual stack network to a WAN, LAN or DMZ port will include IPv4 basic subnet, IPv4 static routing subnet, IPv6 basic subnet and IPv6 static routing subnet.
Auto addressing
FortiWAN supports auto addressing on each of the WAN, LAN and DMZ ports, so that hosts in any of the connected basic subnet can be automatically assigned IP addresses and relative information. FortiWAN provides the addressing mechanisms including DHCP, DHCP relay, DHCPv6 and SLAAC (see Automatic addressing within a basic subnet).
Configuring your WAN and DMZ
In this section we will talk about the configurations for WAN and DMZ network deployments. To have a FortiWAN accessing to the Internet, it requires an ISP network connected to the FortiWAN. The connectivity between a FortiWAN’s WAN port and an ISP network is called a WAN link, which is the necessary medium for accessing the Internet. FortiWAN’s DMZ is designed to be associated with a WAN link, therefore, configuration of a DMZ must be included in a WAN link.
Compared with a LAN network, there are more concerns need to be taken care of for a WAN link and its DMZ. Besides port mapping for the WAN ports on a FortiWAN, you need to decide the WAN types and the subsequent subnet deployments for a WAN link as well. Generally, ISP provides a connectivity in various ways. Here is a table telling what you will have from ISP for a connectivity in different types:
FortiWAN supports WAN links in both routing mode and bridge mode (See WAN types: Routing mode and Bridge mode).
| Internet connectivity type | IP type | No. of IP | Network scale | Modem type |
| Routing Mode | Static | Multiple | An IP subnet (number of available IP matches the netmask) | A gateway (router) |
| Bridge Mode: One
Static IP |
Static | Single | One IP of a large-scale subnet (less number of available IP than the netmask) | A bridge, not a gateway |
| Bridge Mode: Multiple Static IP | Static | Multiple | An IP range of a large-scale subnet (less number of available IP than the netmask) | A bridge, not a gateway |
| Bridge Mode: PPPoE | Dynamic | Single | One IP of a large-scale subnet | A bridge, not a gateway |
| Bridge Mode: DHCP
Client |
Dynamic | Single | One IP of a large-scale subnet | A bridge, not a gateway |
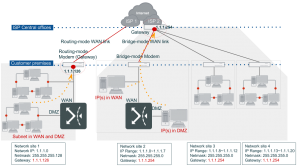
Since ISP provides the available IP addresses in different ways for the above Internet connectivity, FortiWAN has equal mechanisms to identify the near WAN areas and define the static route. Before continuing on the topic, let us review what a near WAN is to FortiWAN first. As previous descriptions, FortiWAN defines the area that is between a FortiWAN’s WAN port and the ISP’s modem as a near WAN of the WAN link. Individual IP addresses, segments and subnets deployed within this area are considered the near WAN of a WAN link. Opposite to the WAN area (the Internet), although near WAN is located on the WAN side, it can be considered as a part of your network site, just like the LAN and DMZ areas. Within the network site, FortiWAN delivers packets among the near WAN, DMZ and LAN according to the static routes. Services of load balancing, fail-over, traffic shaping and statistics (Auto Routing, Bandwidth Management and NAT) will not be applied to those packets. Only packets that are destined to somewhere not defined in the routing table (the traffic communicating with hosts out of the site) will be handled by Bandwidth Management, Auto Routing and NAT, and forwarded to the gateway (the Internet). Note that traffic within near WAN and traffic communicating with near WAN will not be counted in outbound and inbound traffic of the WAN link, but they do occupy part of bandwidth of the WAN link. You should be careful about usage of your near WAN. A lot of near WAN traffic impacts on FortiWAN’s WAN load-balancing and traffic shaping.
Configurations of WAN links are mainly about setting the static routing information to FortiWAN for the near WAN
(and DMZ). Comparing with a LAN, setting the static route for near WAN and DMZ of a WAN link is more complex and variable. According to the distinguishing characteristics of different WAN types, FortiWAN identifies the near WAN and DMZ areas of a WAN link in different ways. Configuring a WAN link as a unsuitable type on FortiWAN will result in a mistake for near WAN identification; miscalculation and misjudgment then happen when performing traffic statistics, traffic shaping and load-balancing. The followings are the mechanisms FortiWAN uses for different WAN types:
| Routing-mode WAN link | l | It requires at least one IPv4 network being configured for a IPv4-based Internet connectivity, or a pair of IPv4 and IPv6 networks for a dual-stack connectivity. |
| l | Any IP address of the network is considered either in near WAN or DMZ (except the IP used by localhost). | |
| l | The whole IPv4/IPv6 network (indicated by the specified netmask) is considered belonging to your site, either in form of a near WAN or a combination of near WAN and DMZ. | |
| l | A near WAN is considered an IPv4/IPv6 network and the gateway of the WAN link is counted in the near WAN. | |
| l | Traffic that matches routing entries of the network will bypass Bandwidth Management and Auto Routing. If a bridge-mode Internet connectivity is incorrectly configured as a routing-mode WAN link on FortiWAN, all the IP addresses of the network (usually a large-scale network such as a class C) will be considered belonging to your site. However, the problem is that most of the IP addresses do not actually belong to your site (they are outside of your site, over the Internet); WAN load-balancing, fail-over and traffic shaping should not be bypassed for those traffic. | |
| Bridge-mode WAN link with multiple static IP | l | It requires exactly specifying the individual IPv4/IPv6 address or IPv4/IPv6 ranges to deploy near WAN and/or DMZ for a IPv4-based or dual-stack WAN link. |
| l | Only the specified IPv4/IPv6 addresses are considered belonging to your site (located in near WAN or DMZ). Unspecified IP addresses are considered the outside of your site, belonging to the Internet. | |
| l | A near WAN is considered a segment of an IPv4/IPv6 network. The gateway of the WAN link will not be count in the near WAN. | |
| l | Incorrectly configuring a routing-mode Internet connectivity as a bridge-mode WAN link on FortiWAN will result in abnormal behaviors to traffic communicating with the gateway and unspecified IP addresses. | |
| Bridge-mode WAN link with one static IP
PPPoE bridge-mode WAN link DHCP bridge-mode WAN link |
l l | Near WAN and DMZ are not supported for this WAN type on FortiWAN. Only the IPv6/IPv4 address assigned to localhost of the WAN link is considered belonging to your site. All the other IP addresses (including the gateway) within the same network (indicated by the specified netmask) are considered the outside of your site. |
| l | Incorrectly configuring a routing-mode Internet connectivity as a bridge-mode WAN link on FortiWAN will result in abnormal behaviors to traffic communicating with the gateway and unspecified IP addresses. |
You have to figure out the type of your link, so that you can correctly configure it to FortiWAN. The netmask and number of IP addresses indicate whether you have an complete IP subnet (routing mode) or just some IP addresses of a large-scale subnet (bridge mode). If you have ISP links belonging to Routing Mode and Bridge Mode: Multiple Static IP, you will have more than one IP address to use. The localhost of a WAN port will require one IP address, and the rest of the IP addresses are available to hosts connected to the WAN port and a DMZ port. Deploying IP addresses to WAN and DMZ are so that included in configurations of Routing Mode and Bridge Mode: Multiple Static IP. As for links belonging to Bridge Mode: One Static IP, Bridge Mode: PPPoE and Bridge Mode: DHCP Client, the only IP address must be used by the localhost of the WAN port and there will be no more IP addresses available to other hosts in WAN and DMZ.
[WAN Settings] is the major part to deploy FortiWAN in various types of WAN links. If your network has several WAN links, you have to configure one after another. Select any link from [WAN link] and check [Enable] to start a configuration of the WAN connection (See “WAN link and WAN port”). A configuration of WAN link is divided into three parts: Basic Settings, Basic Subnet and Static Routing Subnet. Before starting configuration, here are several important concepts you should know.
Configuration of a WAN link, no matter what the WAN type it is, contains the following parts:
Basic setting
The basic setting will require you to set the maximum upload/download bandwidth of a WAN link, upload/download threshold and the MTU for transmission between FortiWAN and ISP’s network. These settings are necessary for FortiWAN Bandwidth Management (see Bandwidth Management), Auto Routing (see Auto Routing) and Multihoming (Multihoming) refer to process the real WAN traffic that is between FortiWAN and the Internet (traffic between FortiWAN and its near WAN is not included).
For bridge-mode WAN links, the basic setting also contains extra fields:
Bridge Mode: One Static IP
Allocating the only IPv4/IPv6 address to localhost of the WAN port.
Bridge Mode: Multiple Static IP
Allocating the one IPv4/IPv6 address to localhost of the WAN port, and arrange others to network segments in WAN and/or DMZ if necessary. Opposite to routing-mode WAN links, ISP provides you a range of IP addresses of a large-scale network for the bridge-mode WAN link, not a network subnet. These IP addresses can be deployed in WAN and/or DMZ, and the corresponding static roue will be established as well, but it is just not a basic subnet (in routing-mode, IP addresses of a WAN link in WAN and/or DMZ are treated as )
Bridge Mode: PPPoE
The username and password for PPPoE accessing.
IPv4/IPv6 basic subnet & IPv4/IPv6 static routing subnet
As previous description, FortiWAN need the static rout to find path for traffic among LAN, DMZ and near WAN. When you configure a routing-mode WAN link or an IPv4/IPv6 dual stack link, settings of basic subnet and static routing subnet are the route to FortiWAN for IPv4/IPv6 networks connecting to WAN ports and/or DMZ ports.
Routing mode and Bridge mode: multiple static IP
Routing mode and bridge mode (multiple static IP) deploy IP addresses in WAN and DMZ in different ways. The following table lists the difference between the two modes for the WAN link deployments.
| Routing mode | Bridge mode: Multiple static IP | |
| Form of given IPs and netmask | An IP subnet (Number of IP matches scale of the netmask) | A range of IPs (Number of IP is less than scale of the netmask) |
| Routing mode | Bridge mode: Multiple static IP | |
| Gateway | Located on customer premises | Located on ISP’s central office |
| Modem type | Functions as a router (the gateway) | Functions as a bridge |
| Deployment of near WAN and/or DMZ | Supports | Supports |
| Static routing subnets in near WAN and/or DMZ | Supports | Not supports |
| Configuration for near WAN and/or DMZ | In Basic Subnet and Static Routing Subnet | In Basic Setting |
Start to configure a WAN link
To deploy a WAN link on FortiWAN, go to System > Network Setting and expand WAN Setting panel on the Web UI. Configurations of all the WAN links start from a common setting block in the panel:
| WAN Link | Select the WAN link that you are configuring to FortiWAN from the drop-down menu. Depending on the model, FortiWAN supports up to 25 or 50 WAN links. All the WAN links are numbered from 1 to 25 or 50, such as WAN link 1, WAN link 2, … and WAN link 50. Each number indicates a WAN link. The number is nothing about the WAN port that the WAN link is installed to. For example, you can install WAN link 1 to WAN Port 3, or WAN link 3 to WAN Port 1.
Number of WAN links that a FortiWAN supports is always more than its physical network port. For example, FortiWAN 200B supports 25 WAN links, but 5 physical network ports are provided only. You will need to create VLAN ports on FortiWAN’s ports to install more than 4 WAN links. In configurations of most of FortiWAN’s services, such as Auto Routing, Multihoming , Bandwidth Management, Virtual Server, NAT and etc., these WAN links appear as options for associating policies and rules to a WAN link. They are also the options used to switch among WAN links for statistics. |
| Enable | Check/uncheck to enable/disable the WAN link. Enabling/disabling of a WAN link does not represent the connectivity status of the WAN link. Connectivity statuses of the enabled WAN links will be listed in in WAN Link State panel on Web UI page System > Summary. |
| Note | Text descriptions for the WAN link. You can see the notes of the enabled WAN link in WAN Link State panel on Web UI page System > Summary. |
WAN Type
The first step to start a WAN link configuration is deciding the WAN type (See “WAN types: Routing mode and Bridge mode”). Configuration varies on [WAN Type] in [Basic Settings]. The [WAN Type] could be one of:
l Routing Mode (See “Configurations for a WAN link in Routing Mode”) l Bridge Mode: One Static IP (See “Configurations for a WAN link in Bridge Mode: One Static IP”) l Bridge Mode: Multiple Static IP (See “Configurations for a WAN link in Bridge Mode: Multiple Static IP”) l Bridge Mode: PPPoE (See “Configurations for a WAN link in Brideg Mode: PPPoE”) l Bridge Mode: DHCP Client (See “Configurations for a WAN link in Bridge Mode: DHCP”)
See also
- WAN link and WAN port
- Configurations for a WAN link in Routing Mode
- Configurations for a WAN link in Bridge Mode: One Static IP
- Configurations for a WAN link in Bridge Mode: Multiple Static IP
- Configurations for a WAN link in Brideg Mode: PPPoE
- Configurations for a WAN link in Bridge Mode: DHCP