WCCP configuration overview
To configure WCCP you must create a service group that includes WCCP servers and clients. WCCP servers intercept sessions to be cached (for example, sessions from users browsing the web from a private network). To intercept sessions to be cached the WCCP server must include a security policy that accepts sessions to be cached and WCCP must be enabled in this security policy.
The server must have an interface configured for WCCP communication with WCCP clients. That interface sends and receives encapsulated GRE traffic to and from WCCP clients. The server must also include a WCCP service group that includes a service ID and the addresses of the WCCP clients as well as other WCCP configuration options.
To use a FortiGate unit as a WCCP client, the FortiGate unit must be set to be a WCCP client (or cache engine). You must also configure an interface on the client for WCCP communication. The client sends and receives encapsulated GRE traffic to and from the WCCP server using this interface.
The client must also include a WCCP service group with a service ID that matches a service ID on the server. The client service group also includes the IP address of the servers in the service group and specifies the port numbers and protocol number of the sessions that will be cached on the client.
When the client receives sessions from the server on its WCCP interface, it either returns cached content over the WCCP interface or connects to the destination web servers using the appropriate interface depending on the client routing configuration. Content received from web servers is then cached by the client and returned to the WCCP server over the WCCP link. The server then returns the received content to the initial requesting user web browser.
Finally you may also need to configure routing on the server and client FortiGate units and additional security policies may have to be added to the server to accept sessions not cached by WCCP.
Example caching HTTP sessions on port 80 using WCCP
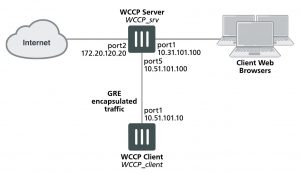
In this example configuration (shown below), a FortiGate unit with host name WCCP_srv is operating as an Internet firewall for a private network is also configured as a WCCP server. The port1 interface of WCCP_srv is connected to the Internet and the port2 interface is connected to the internal network.
All HTTP traffic on port 80 that is received at the port2 interface of WCCP_srv is accepted by a port2 to port1 security policy with WCCP enabled. All other traffic received at the port2 interface is allowed to connect to the Internet by adding a general port2 to port1 security policy below the HTTP on port 80 security policy.
A WCCP service group is added to WCCP_srv with a service ID of 0 for caching HTTP traffic on port 80. The port5 interface of WCCP_srv is configured for WCCP communication.
A second FortiGate unit with host name WCCP_client is operating as a WCCP client. The port1 interface of WCCP_client is connected to port5 of WCCP_srv and is configured for WCCP communication.
WCCP_client is configured to cache HTTP traffic because it also has a WCCP service group with a service ID of 0.
WCCP_client connects to the Internet through WCCP_srv. To allow this, a port5 to port1 security policy is added to WCCP_srv.
FortiGate WCCP server and client configuration
Configuring the WCCP server (WCCP_srv)
Use the following steps to configure WCCP_srv as the WCCP server for the example network. The example steps only describe the WCCP-related configuration.
To configure WCCP_srv as a WCCP server
1. Add a port2 to port1 security policy that accepts HTTP traffic on port 80 and is configured for WCCP:
config firewall policy edit 0
set srtintf port2 set dstintf port1 set srcaddr all set dstaddr all set action accept
set schedule always set service HTTP
set wccp enable set nat enable
end
2. Add another port2 to port1 security policy to allow all other traffic to connect to the Internet.
config firewall policy edit 0
set srtintf port2 set dstintf port1 set srcaddr all set dstaddr all set action accept
set schedule always set service ANY
set nat enable end
3. Move this policy below the WCCP policy in the port2 to port1 policy list.
4. Enable WCCP on the port5 interface.
config system interface edit port5
set wccp enable end
5. Add a WCCP service group with service ID 0.
config system wccp edit 0
set router-id 10.51.101.100
set server-list 10.51.101.0 255.255.255.0 end
6. Add a firewall address and security policy to allow the WCCP_client to connect to the internet.
config firewall address edit WCCP_client_addr
set subnet 10.51.101.10
end
config firewall policy edit 0
set srtintf port5 set dstintf port1
set srcaddr WCCP_client_addr set dstaddr all
set action accept set schedule always set service ANY
set nat enable end
Configuring the WCCP client (WCCP_client)
Use the following steps to configure WCCP_client as the WCCP client for the example network. The example steps only describe the WCCP-related configuration.
To configure WCCP_client as a WCCP client
1. Configure WCCP_client to operate as a WCCP client.
config system settings
set wccp-cache-engine enable end
You cannot enter the wccp-cache-engine enable command if you have already added a WCCP service group. When you enter this command an interface named w.<vdom_name> is added to the FortiGate configuration (for example w.root). All traffic redirected from a WCCP router is considered to be received at this interface of the FortiGate unit operating as a WCCP client. A default route to this interface with lowest priority is added.
2. Enable WCCP on the port1 interface.
config system interface edit port1
set wccp enable
end
3. Add a WCCP service group with service ID 0.
config system wccp edit 0
set cache-id 10.51.101.10
set router-list 10.51.101.100
end