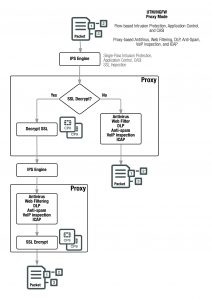
UTM/NGFW packet flow: proxy-based inspection
If a FortiGate or VDOM is configured for proxy-based inspection then a mixture of flow-based and proxy-based inspection occurs. Packets initially encounter the IPS engine, which uses the same steps described in UTM/NGFW packet flow: flow-based inspection on page 1899 to apply single-pass IPS, Application Control and CASI if configured in the firewall policy accepting the traffic.
The packets are then sent to the FortiOS UTM/NGFW proxy for proxy-based inspection. The proxy first determines if the traffic is SSL traffic that should be decrypted for SSL inspection. SSL traffic to be inspected is decrypted by the proxy. SSL decryption is offloaded to and accelerated by CP8 or CP9 processors.
Proxy-based inspection extracts and caches content, such as files and web pages, from a content session and inspects the cached content for threats. Content inspection happens in the following order: VoIP inspection, DLP, AntiSpam, Web Filtering, Antivirus, and ICAP.
If no threat is found the proxy relays the content to its destination. If a threat is found the proxy can block the threat and replace it with a replacement message.
Decrypted SSL traffic is sent to the IPS engine (where IPS, Application Control, and CASI can be applied) before re-entering the proxy where actual proxy-based inspection is applied to the decrypted SSL traffic. Once decrypted SSL traffic has been inspected it is re-encrypted and forwarded to its destination. SSL encryption is offloaded to and accelerated by CP8 or CP9 processors. If a threat is found the proxy can block the threat and replace it with a replacement message.
The proxy can also block VoIP traffic that contains threats. VoIP inspection can also look inside VoIP packets and extract port and address information and open pinholes in the firewall to allow VoIP traffic through.
ICAP intercepts HTTP and HTTPS traffic and forwards it to an ICAP server. The FortiGate is the surrogate, or “middle-man”, and carries the ICAP responses from the ICAP server to the ICAP client; the ICAP client then responds back, and the FortiGate unit determines the action that should be taken with these ICAP responses and requests.
Comparison of inspection types
The tables in this section show how different security functions map to different inspection types.
Mapping security functions to inspection types
The table below lists FortiOS security functions and shows whether they are applied by the kernel, flow-based inspection or proxy-based inspection.
FortiOS security functions and inspection types
Security Function Kernel
(Stateful inspection)
Flow–based inspection Proxy-based inspection
Firewall yes
IPsec VPN yes
Traffic Shaping yes
User Authentication yes
Management Traffic yes
SSL VPN yes
IPS yes
Antivirus yes yes
Application Control yes
CASI yes
Web filtering yes yes
DLP yes yes
Email Filtering yes
VoIP inspection yes
ICAP yes
More information about inspection methods
The three inspection methods each have their own strengths and weaknesses. The following table looks at all three methods side-by-side.
Inspection methods comparison
Feature Stateful Flow Proxy
Inspection unit per ses- sion
first packet selected packets, single pass architecture, sim- ultaneous application of configured inspection methods
complete content, con- figured inspection meth- ods applied in order
Feature Stateful Flow Proxy
Memory, CPU required low medium high
Level of threat protection good better best
Authentication yes
IPsec and SSL VPN yes
Antivirus protection yes yes
Web Filtering yes yes
Data Leak Protection (DLP)
yes yes
Application control yes
IPS yes
Delay in traffic minor no small
Reconstruct entire con- tent
no yes