Bridge-mode (multiple static IP) WAN link
Configuration of a multiple-static-IP bridge-mode WAN link starts from selecting and enabling the WAN link on
Web UI (see Start to configure a WAN link in Configuring your WAN and DMZ), and select Bridge Mode: Multiple Static IP from the WAN Type drop-down menu in Basic Setting panel. After that, you start configuring the following settings:
IPv4-based bridge-mode WAN link l Only Basic setting is necessary.
- IPv4 basic subnets and IPv4 static routing subnets are not supported here. IPv4/IPv6 Dual-stack bridge-mode WAN link l Only Basic setting is necessary.
- IPv4 basic subnets and IPv4 static routing subnets are not supported here; IPv6 basic subnets and IPv6 static routing subnets are optional.
Different from routing mode, configuration of static routing is contained in Basic Setting for a bridge-mode WAN link. Similar to routing mode, FortiWAN uses ProxyARP to combine the WAN area and DMZ area as one logical network segment.
Basic Setting
Besides the WAN Type, the rest setting fields of Basic Setting of a multiple-static-IP bridge-mode WAN link are as followings:
| WAN Port A FortiWAN’s network port used to connect the WAN link with the FortiWAN (you need to physically install the network cable to this port for the WAN link). All the physical and VLAN ports that are mapped to WAN (see Aggregated, Redundant, VLAN Ports and Port Mapping) are listed here for your options. The WAN link field is unrelated to the WAN port. For example, you can install WAN link 1 to WAN Port3, or WAN link 3 to WAN Port 1. (See WAN link and WAN port). | |
| Up/Down Stream The WAN link’s transfer speed at which you can download/upload data from/to
the Internet. Please input the value in Kbps, e.g. 10240Kbps/640Kbps. FortiWAN Bandwidth Management’s default inbound and outbound classes use the two values actively to limit the download and upload rates on the WAN link (see Bandwidth Management). |
|
| Up/Down Stream Threshold Specify upstream/downstream (Kbps) threshold to the WAN link. WAN links with traffic exceeding the thresholds will be considered as failed.
FortiWAN’s Auto Routing and Multihoming will ignore the WAN links failed by exceeding traffic while distributing traffic over WAN links, if the Threshold function is enabled in their load-balancing policies (See Outbound Load Balancing and Failover (Auto Routing) and Inbound Load Balancing and Failover (Multihoming)). Leave it blank or zero if you do not apply threshold to the WAN link. |
|
| MTU (Maximum Transmission unit) refers to the size of the largest packet or frame that a given layer of a communications protocol can pass onwards on the WAN port. It allows dividing the packet into pieces, each small enough to pass over a single link. It is set to 1500 by default. | |
| IPv4 IP(s) on Localhost The IPv4 addresses that are deployed on localhost (See “Scenarios to deploy
subnets”). IP addresses specified here can be used for NAT to transfer the source IP address of packets to. The first IP address listed here will be used to generate the NAT default rules of the WAN link (See “NAT”). |
|
| IPv4 IP(s) in WAN The IPv4 addresses that are deployed in WAN. | |
| IPv4 IP(s) in DMZ The IPv4 addresses that are deployed in DMZ. | |
| Different from configuration of Routing mode’s basic subnets, it requires exactly specifying IPs to fields IP(s) in WAN and IP(s) in DMZ for a Bridge mode WAN link if you want to deploy those IP addresses in the WAN and DMZ areas. FortiWAN would not automatically classifies the rest IPs of a subnet as IPs in WAN or IPs in DMZ for bridge-mode
WAN links (FortiWAN does it for a routing-mode WAN link), since the bridge mode is supposed to work with certain IPs of a large-scale network (see WAN types: Routing mode and Bridge mode) and FortiWAN is not aware of what the IPs are that an ISP provides you for the WAN link (the remaining IPs of the large-scale subnet are not valid to be deployed in your network). |
|
| IPv4 Netmask | The IPv4 netmask that ISP provides. |
| IPv4 Gateway | The IPv4 address of the default gateway. |
| IPv6 IP(s) on Localhost | The IPv6 addresses that are deployed on localhost (See “Scenarios to deploy subnets”). IP addresses specified here can be used for NAT to transfer the source IP address of packets to. The first IP address listed here will be used to generate the NAT default rules of the WAN link. For FortiWAN V4.0.x, system does not generate NAT default rules for IPv6 WAN links, setting NAT rules manually is required (See “NAT”). |
| IPv6 IP(s) in WAN | The IPv6 addresses that are deployed in WAN. |
| IPv6 IP(s) in DMZ | The IPv6 addresses that are deployed in DMZ. |
| IPv6 Prefix | The IPv6 prefix that ISP provides. |
| IPv6 Gateway | The IPv6 address of the default gateway. |
| Subnet | The IPv6 subnet deployed on the WAN link. |
| DMZ Port | The network port of FortiWAN used to connect the DMZ area. All the physical and logical ports that are mapped to DMZ (see Configurations for VLAN and Port Mapping) are listed here for options. Hosts deployed in the DMZ are required to connected to this port. Public IP pass-through (see Public IP Pass-through) is supported to combine the selected WAN port and DMZ port. |
| Enable DHCP/DHCP
Relay/SLAAC/DHCPv6 Service |
Click to enable automatic addressing on the specified DMZ port for hosts in the connected IPv4/IPv6 DMZ segment (see Automatic addressing within a basic subnet for configuration details).
Note that only the IP addresses defined in fields IPv4 IP(s) in DMZ and IPv6 IP(s) in DMZ are the candidates for related IP pools of automatic addressing. |
The SLAAC and DHCPv6 in FortiWAN are designed to work together, which the SLAAC responses router advertisement (including default gateway and DNS server) to a host and DHCPv6 responses the host an appropriate IPv6 address.
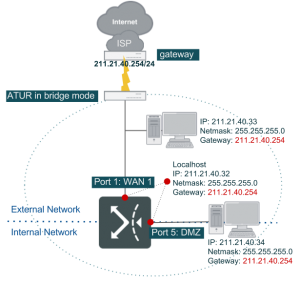
This topology can be seen where a group of valid IP addresses ranging 211.21.40.32~211.21.40.34 have been given by ISP and assigned to port1 on FortiWAN. And their default gateway is 211.21.40.254 given by ISP as well. If there are other hosts deployed on the WAN, then configure their IP addresses in [IP(s) in WAN]. And if there are hosts deployed on the DMZ, then configure their IP addresses in [IP(s) in DMZ].
| Basic Setting | |
| WAN Port | Port1 |
| IPv4 IP(s) on Localhost | 211.21.40.32 |
| IPv4 IP(s) in WAN | 211.21.40.33 |
| IPv4 IP(s) in DMZ | 211.21.40.34 |
| IPv4 Netmask | 255.255.255.0 |
| IPv4 Gateway | 211.21.40.254 |
| DMZ Port | Port5 |
Static routing information
FortiWAN assumes that the near WAN and DMZ areas of a bridge-mode WAN link (both of IPv4-based and dualstack) are parts of a large-scale network, not a complete network, with the exception of extra IPv6 subnets being available for dual-stack WAN links. Static routing information is set to FortiWAN by assigning individual IP in Basic Setting, rather than specifying a network in Basic Subnet. FortiWAN’s bridge-mode accepts complete IPv6 networks to be deployed to the DMZ. In case that ISP provides multiple IPv6 subnets for a dual-stack connectivity, it is an option for you to use. Configurations of IPv6 basic subnets and IPv6 static routing subnets are so that the routing information for the FortiWAN.
[IPv6 Basic Subnet]: Subnet in DMZ
This is the only type that FortiWAN provides for basic subnets of a bridge-mode WAN link. Click the add button on the IPv6 Basic Subnet panel to add a configuration, and select Subnet in DMZ from the Subnet Type drop-down menu. The rest configuration fields are as followings:
| IP(s) on Localhost | The IP address(es) of the IPv6 network that you want to assign to localhost of the specified DMZ port (the DMZ port that is specified below) of the WAN link. At least one IP address is required here. You can type a range of IP addresses here in format “IPstart-IPend” or click the add button to individually add more IP addresses to the localhost.
Note that the rest IP addresses of the network that are not assigned to the localhost here will be automatically considered as being located in DMZ area. |
| Prefix Length | Prefix Length of the IPv6 network that is being deployed as a subnet in DMZ and associated with the WAN link. |
| DMZ Port | A FortiWAN’s network port used to connect a subnet of the WAN link with the FortiWAN as a DMZ subnet (you need to physically install the network cable to this port for the DMZ subnet). All the physical, logical and VLAN ports that are mapped to DMZ (see Aggregated, Redundant, VLAN Ports and Port Mapping) are listed here for your options. |
| Enable SLAAC/DHCPv6
Service |
Click to enable automatic addressing on the specified DMZ port for hosts in the connected IPv6 DMZ subnet (see Automatic addressing within a basic subnet for configuration details).
Note that only the IP addresses of the IPv6 basic subnet defined here are the candidates for related IP pools of automatic addressing. |
[IPv6 Static Routing Subnet]: Subnet in DMZ
This is the only type that FortiWAN provides for static routing subnets of a bridge-mode WAN link. Click the add button on the IPv6 Static Routing Subnet panel to add a configuration, and select Subnet in DMZ from the Subnet Type drop-down menu. The rest configuration fields are as followings:
| Subnet | The IPv6 static routing subnet that you want to deploy in DMZ area of the WAN link in format such as 2000::123f:0:0:1/32. |
| Gateway | IPv6 address of the gateway (router) connecting a basic subnet with the static routing subnet. This IP address is the path that FortiWAN uses to forward packets destined to the static routing subnet to. |
See also
- WAN link and WAN port
- VLAN and port mapping
- Configurations for VLAN and Port Mapping
- Outbound Load Balancing and Failover (Auto Routing)
- Inbound Load Balancing and Failover (Multihoming)
- Scenarios to deploy subnets
- Public IP pass through (DMZ Transparent Mode)
- IPv6/IPv4 Dual Stack
Having trouble configuring your Fortinet hardware or have some questions you need answered? Check Out The Fortinet Guru Youtube Channel! Want someone else to deal with it for you? Get some consulting from Fortinet GURU!