Hub–and–spoke configurations
This section describes how to set up hub-and-spoke IPsec VPNs. The following topics are included in this section: Configuration overview
Configure the hub
Configure the spokes
Dynamic spokes configuration example
Configuration overview
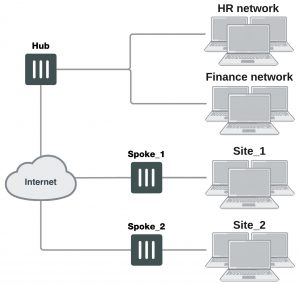
In a hub-and-spoke configuration, VPN connections radiate from a central FortiGate unit (the hub) to a number of remote peers (the spokes). Traffic can pass between private networks behind the hub and private networks behind the remote peers. Traffic can also pass between remote peer private networks through the hub.
Example hub-and-spoke configuration
The actual implementation varies in complexity depending on:
- Whether the spokes are statically or dynamically addressed
- The addressing scheme of the protected subnets
- How peers are authenticated
This guide discusses the issues involved in configuring a hub-and-spoke VPN and provides some basic configuration examples.
Hub–and–spoke infrastructure requirements
- The FortiGate hub must be operating in NAT mode and have a static public IP address.
- Spokes may have static IP addresses, dynamic IP addresses (see FortiGate dialup-client configurations on page 1716), or static domain names and dynamic IP addresses (see Dynamic DNS configuration on page 1688).
Spoke gateway addressing
The public IP address of the spoke is the VPN remote gateway as seen from the hub. Statically addressed spokes each require a separate VPN Phase 1 configuration on the hub. When there are many spokes, this becomes rather cumbersome.
Using dynamic addressing for spokes simplifies the VPN configuration because then the hub requires only a single Phase 1 configuration with “dialup user” as the remote gateway. You can use this configuration even if the remote peers have static IP addresses. A remote peer can establish a VPN connection regardless of its IP address if its traffic selectors match and it can authenticate to the hub. See Configuration overview on page 1671 for an example of this configuration.
Protected networks addressing
The addresses of the protected networks are needed to configure destination selectors and sometimes for security policies and static routes. The larger the number of spokes, the more addresses there are to manage. You can
- Assign spoke subnets as part of a larger subnet, usually on a new network or
- Create address groups that contain all of the needed addresses
Having trouble configuring your Fortinet hardware or have some questions you need answered? Check Out The Fortinet Guru Youtube Channel! Want someone else to deal with it for you? Get some consulting from Fortinet GURU!